
- Name: NoName057(16)
- Type: Hacktivist Collective
- First Seen (DarkWebSonar): October 2024
- Last Seen: January 2026
- Primary Activity: DDoS
- Primary Region: Europe
- Risk Level: High
Executive Summary
NoName057(16) is currently the most active threat actor tracked by DarkWebSonar, responsible for sustained, near-daily DDoS operations targeting European governments and critical infrastructure. Unlike hacktivist groups that operate in short-lived bursts, NoName057(16) maintains consistent operational tempo, often launching multiple attacks per day across different countries and sectors.
DarkWebSonar telemetry shows that the group’s activity is heavily concentrated in Europe and the United Kingdom, with government administration, transportation, energy, and telecommunications organizations bearing the brunt of the disruption. As of early 2026, activity levels remain stable and persistent, positioning NoName057(16) as a high-risk pressure actor rather than a campaign-driven threat.
By the Numbers (DarkWebSonar Telemetry)
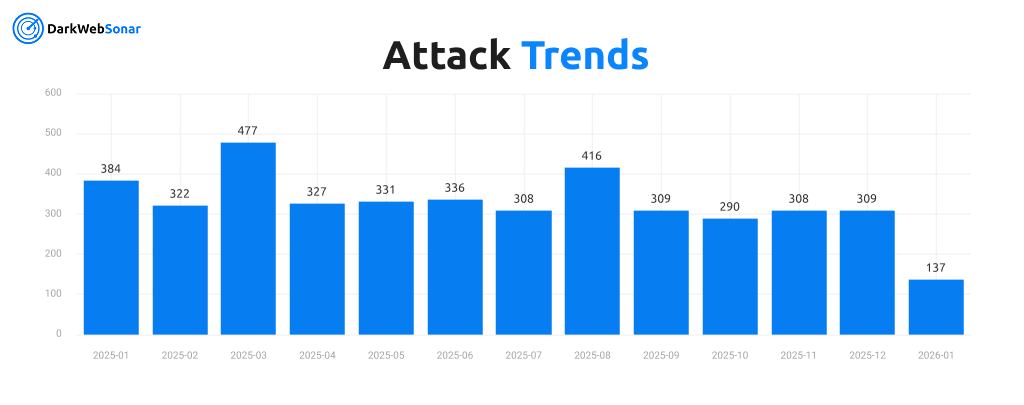
- Total incidents tracked (Oct 2024–Jan 2026): 5,516
- Incidents (last 90 days): 894
- Average activity: 10–20 incidents per day
- Peak activity: March, 2025 (477 incidents)
- Days active: 470+ out of 470 days tracked
NoName057(16)’s activity volume and consistency exceed that of any other hacktivist collective currently monitored by DarkWebSonar.
Targeting Profile
Top Targeted Countries

- Germany: 538 incidents
- France: 492 incidents
- Italy: 487 incidents
- Belgium: 398 incidents
- Poland: 321 incidents
- United Kingdom: 229 incidents
While Ukraine remains the single most targeted country overall, European Union member states and the UK collectively account for the majority of observed activity, making NoName057(16) especially relevant for European security teams.
Top Targeted Industries
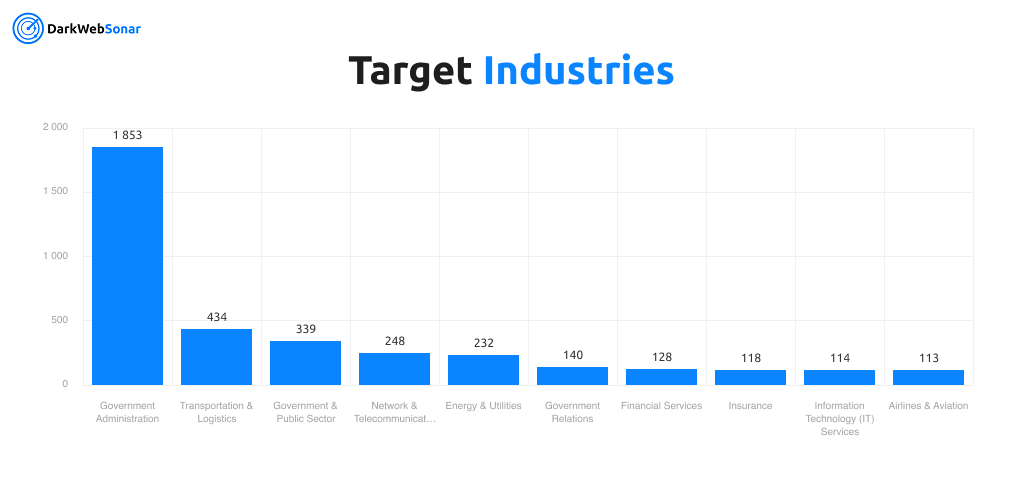
- Government Administration: 1,853 incidents (33.6%)
- Transportation & Logistics: 434 incidents
- Government & Public Sector: 339 incidents
- Network & Telecommunications: 248 incidents
- Energy & Utilities: 232 incidents
- Government Relations: 140 incidents
This distribution reflects a deliberate strategy focused on maximum disruption and visibility, rather than financial gain or long-term system compromise.
Attack Profile & Tactics
- Primary attack type: Distributed Denial-of-Service (DDoS)
- Attack type dominance: 98.8% of all observed incidents
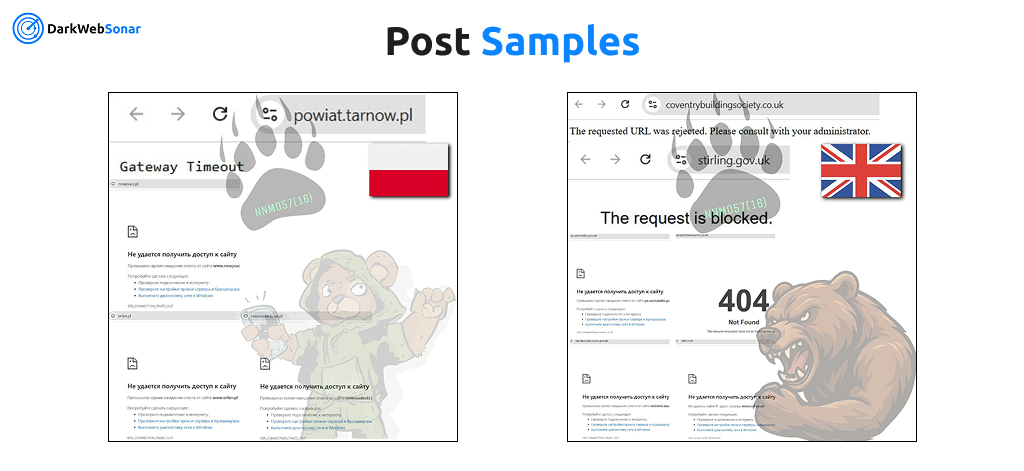
- Coordination method: Telegram-based announcements and proof-of-attack posts
- Operational cadence: Sustained daily operations
- Victim interaction: Public claims, screenshots, and service disruption assertions
The group’s reliance on DDoS underscores a tactical preference for disruption over persistence, with little evidence of data theft, lateral movement, or prolonged access.
Origins & Motivation
Open-source intelligence places NoName057(16)’s ideological roots in the early phases of the Russia–Ukraine conflict, where it emerged as a politically motivated, pro-Russian hacktivist collective communicating primarily through Telegram.
Rather than pursuing financial extortion, the group frames its activity as retaliatory and symbolic, selecting targets based on geopolitical alignment. Countries and organizations perceived as supporting Ukraine or NATO consistently feature in their campaigns, often coinciding with political announcements or international events.
This ideological positioning explains the group’s sustained focus on European government institutions and critical infrastructure, as well as its resilience despite repeated disruptions.
Notable Campaigns
- European Government Portals – Repeated DDoS campaigns against national and regional government websites across Germany, France, Italy, and Belgium
- Transportation Networks – Disruption attempts targeting railways, airports, and logistics providers
- Energy & Utilities – Sustained pressure against European energy infrastructure
- Telecommunications Providers – Attacks aimed at network operators to amplify downstream impact
These campaigns prioritize visibility and operational disruption, often repeating across multiple days.
DarkWebSonar Insights
Continuous monitoring reveals several characteristics that distinguish NoName057(16) from other hacktivist actors:
- Unmatched activity volume: 894 incidents in 90 days
- Exceptional consistency: Daily operations with minimal downtime
- European concentration: Over 3,000 incidents targeting EU member states and the UK
- Telegram-driven operations: Nearly all incidents originate from coordinated Telegram activity
Unlike episodic hacktivist campaigns, NoName057(16) behaves as a persistent pressure actor, creating ongoing operational risk rather than isolated incidents.
Law Enforcement Pressure & Resilience
In mid-2025, an international law-enforcement effort commonly referred to as Operation Eastwood targeted NoName057(16)’s infrastructure, resulting in server seizures, arrests, and public warnings to participants.

Despite this disruption, DarkWebSonar telemetry shows no sustained reduction in activity. The group’s volunteer-driven operational model, rapid infrastructure rotation, and ideological motivation contribute to its resilience and ability to reconstitute operations quickly.
Defender Outlook (2026)
Based on observed behavior, DarkWebSonar assesses that NoName057(16) is likely to:
- Maintain consistent daily DDoS activity throughout 2026
- Continue prioritizing European government and critical infrastructure targets
- Escalate activity in response to geopolitical developments involving Europe and Ukraine
Organizations at highest risk include government agencies, transportation operators, energy providers, and telecommunications firms. While individual attacks are typically short-lived, the cumulative operational burden presents a meaningful security challenge.
Conclusion
NoName057(16) exemplifies how hacktivist collectives can achieve unprecedented scale and persistence through sustained daily operations. With over 5,500 incidents tracked since October 2024, the group has become the most active threat actor observed by DarkWebSonar.
Its intense focus on Europe (combined with operational resilience and ideological motivation) makes NoName057(16) a high-risk, persistent threat for organizations that rely on continuous online availability.
Dark Web Most Wanted profiles are powered by DarkWebSonar’s continuous monitoring of threat actors across dark web forums, leak sites, and Telegram ecosystems.