
- Name: Keymous+
- Type: Hacktivist Collective
- First Seen (DarkWebSonar): November 2024
- Last Seen: February 2026
- Primary Activity: DDoS
- Primary Region: North Africa (primarily Algeria), Middle East, Europe
- Risk Level: High
Executive Summary
Keymous+ has emerged as a high-volume, DDoS-specialist hacktivist collective in DarkWebSonar telemetry, with over 1,400 incidents tracked since late 2024. Nearly 96% of their activity is DDoS attacks, with a strong presence on social media platforms like Telegram and X (formerly Twitter). OSINT research attributes the group to North Africa (primarily Algeria), with origins in late 2023 amid Algeria–Morocco tensions and the Gaza crisis and associations with pro-Palestine hacktivist circles. The group targets a wide geographic spread—from Morocco and France to India, Israel, Egypt, and the UAE, with government, technology, and financial sectors bearing the brunt of their attacks.
DarkWebSonar data shows steady activity patterns and sustained operations into early 2026. Keymous+ presents itself as a hybrid hacktivist group conducting large-scale DDoS attacks, and providing DDoS-for-hire services (e.g. EliteStress), often in collaboration with other actors, positioning them as a persistent disruption threat for organizations in their primary target regions, especially government and critical infrastructure.
By the Numbers (DarkWebSonar Telemetry)
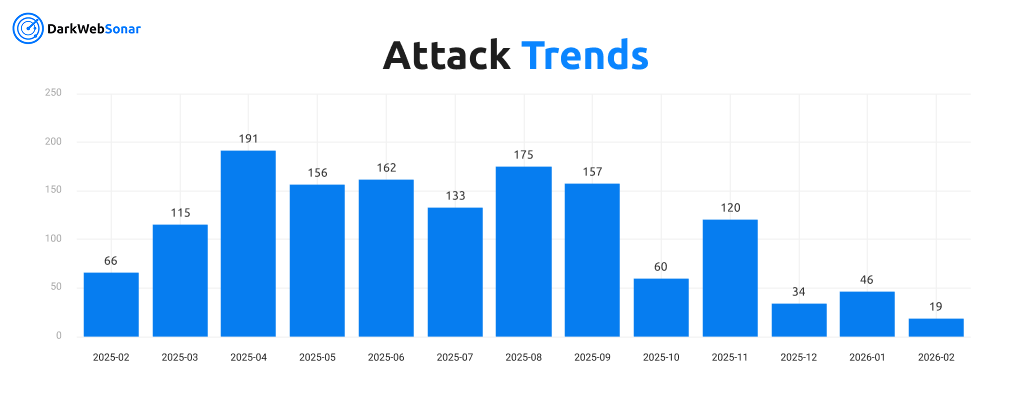
- Total incidents tracked (Nov 2024–Feb 2026): 1,449
- Incidents (last 90 days): 99
- Primary attack type: DDoS (96% of all incidents)
- Secondary activity: Data Breach, Initial Access
- Primary channel: Telegram (1,424 incidents)
- Activity level: Steady; specialist in DDoS
Keymous+ operates as a DDoS specialist with a clear focus on availability disruption rather than long-dwell intrusion or ransomware.
Targeting Profile
Top Targeted Countries
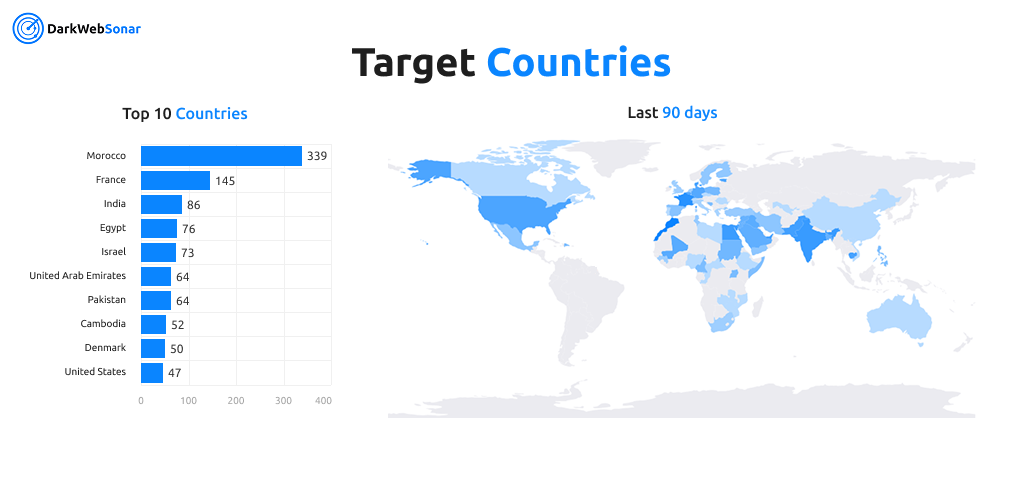
Targeting spans Middle East, North Africa, Europe, and South Asia, with Morocco and France as the two largest victim countries by volume.
Top Targeted Industries
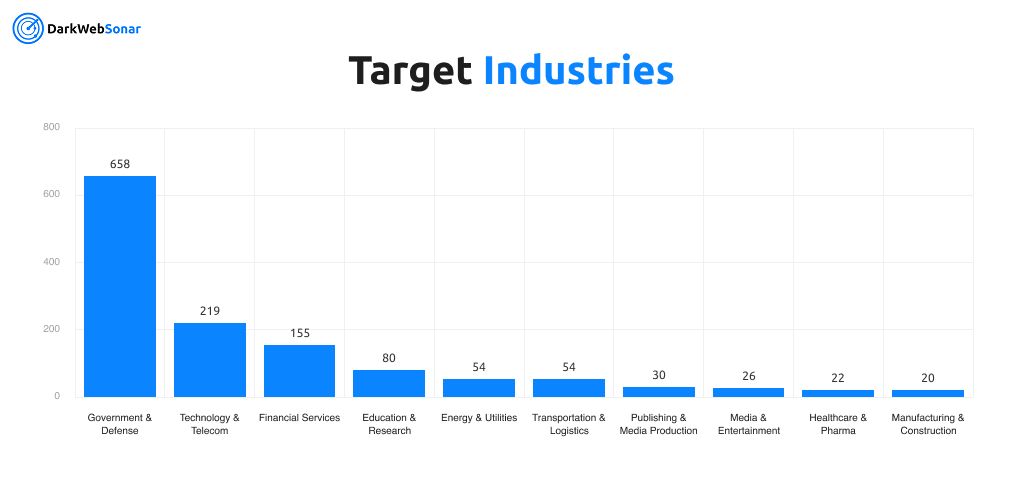
Government and defense dominate, followed by technology, telecom, and financial services—reflecting a mix of symbolic and high-impact targets.
Attack Profile & Tactics
DarkWebSonar telemetry and industry reporting (Netscout ASERT, Cyberpress) characterize Keymous+ as a hybrid hacktivist group conducting large-scale DDoS with diverse techniques and infrastructure:
- Primary attack type: Distributed Denial-of-Service (DDoS) — 96% of incidents in DarkWebSonar
- Reflection/amplification: CLDAP, DNS, memcached, NTP, NetBIOS, rpcbind, SNMP, L2TP, WS-DD, chargen
- Direct floods: DNS query, UDP (including UDP/443), TCP SYN, Layer 7 HTTP
- Spoofing: IP/ASN spoofing via DDoS-for-hire platforms
- Scale: Multivector coordinated attacks with reported peaks of 11.8 Gbps solo and 44 Gbps in collaboration; 42,000+ unique IPs per attack
- Infrastructure: Tor exits, public clouds, compromised IoT/hosts, VPN/proxies
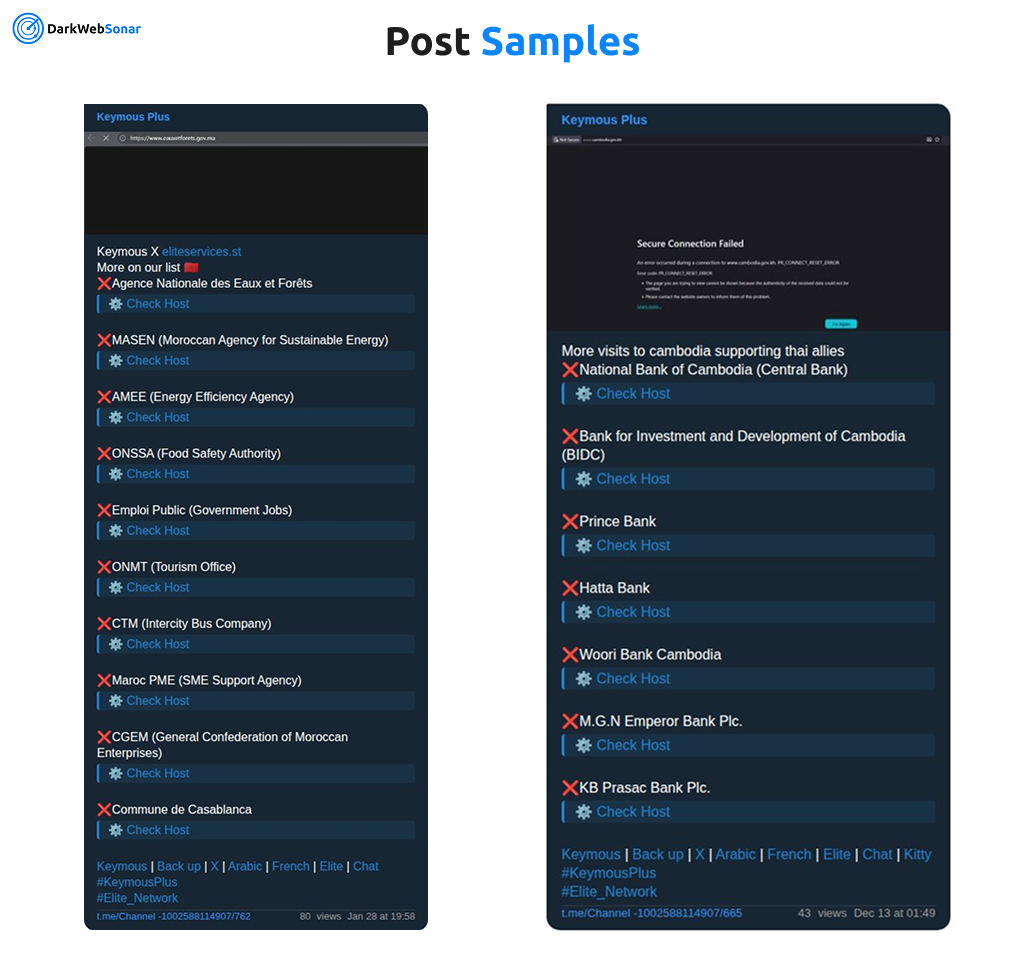
- Tools & coordination: EliteStress DDoS-for-hire; Telegram and X for coordination, recruitment, and proof-of-impact
- Other observed activity: We have observed a few instances of Data breach and initial access claims
- Partnerships: Opportunistic targeting and collaboration with other actors, including DDoS54, NoName057(16), and Mr Hamza
The group’s profile is consistent with disruption-first hacktivism: high-volume, multivector DDoS for availability impact, with limited but present data-centric activity (breaches, leaks) used for visibility and pressure.
Origins & Motivation
Open-source research attributes Keymous+ to Algeria, with medium confidence. The group is reported to have originated in late 2023 amid Algeria–Morocco tensions and the Gaza crisis, with associations to pro-Palestine hacktivist circles. Keymous+ first appeared in DarkWebSonar in November 2024 and has maintained activity through February 2026.
Their geographic spread (heavy focus on Morocco, France, India, Egypt, Israel, UAE, and Pakistan) aligns with politically and ideologically motivated targeting: Morocco as a regional rival (consistent with Algeria–Morocco tensions), Israel and Western or Gulf states as symbolic targets, and India among others in broader hacktivist campaigns (e.g. post–Operation Sindoor, a wave of India-focused DDoS activity by hacktivist coalitions following Indian military strikes in May 2025). Telegram- and X-centric operations and the mix of government, technology, and financial targets reflect a hacktivist collective seeking maximum visibility and disruption across multiple regions, while DDoS-for-hire (EliteStress) adds a commercial dimension to their activity.
Notable Campaigns
- Algeria–Morocco proxy targeting (ongoing): Keymous+ has conducted hundreds of DDoS incidents against Moroccan government, financial, and infrastructure entities (the group's most consistent and voluminous targeting), directly reflecting the Algeria–Morocco geopolitical rivalry that spurred its formation in late 2023.
- Anti-Israel and Western campaigns (ongoing): Sustained attacks against Israeli, French, and Gulf-region targets, consistent with the group's pro-Palestine ideology and alignment with broader Middle East hacktivist coalitions.
- Operation Sindoor response (May–June 2025): Keymous+ participated in a broad hacktivist coalition targeting Indian government and technology infrastructure following Indian military strikes in May 2025, contributing DDoS capacity alongside dozens of other groups.
- Multi-country DDoS waves (September, November 2025): Sustained activity spikes with coordinated multivector attacks across government and financial targets in multiple countries, including collaborative operations with DDoS54, NoName057(16), and Mr Hamza with reported combined peaks of 44 Gbps.
- DDoS-for-hire promotion (ongoing): Active use and promotion of EliteStress and similar DDoS-as-a-service platforms, blurring the line between ideologically motivated hacktivism and profit-driven cybercrime.
Campaigns emphasize broad geographic and sector coverage with a consistent DDoS-centric approach and opportunistic collaboration with other threat actors.
DarkWebSonar Insights
Continuous monitoring and cross-reference with industry reporting highlight what distinguishes Keymous+ from other actors:
- DDoS specialist: 96% of incidents are DDoS, with a clear specialization vs. generalist hacktivist groups; industry reports describe multivector attacks (11.8 Gbps solo, 44 Gbps collaborative) and 42,000+ unique IPs per attack
- Telegram- and X-centric: The vast majority of tracked activity originates from Telegram; X used for coordination and proof-of-impact
- Wide geographic footprint: 50+ victim countries, with concentration in Morocco, France, India, Egypt, and Israel
- Government-heavy targeting: 45% of incidents against government & defense
- Steady activity: Activity level classified as steady, with sustained operations into 2026
- Hybrid model: Combination of ideologically motivated hacktivism (Algeria–Morocco, Gaza, pro-Palestine) and DDoS-for-hire (EliteStress), with partnerships (DDoS54, NoName057(16), Mr Hamza) extending reach and impact
These traits make Keymous+ a relevant threat for organizations in their top target countries and sectors, especially those dependent on public-facing availability.
Defender Outlook (2026)
Based on observed behavior and DarkWebSonar data, Keymous+ is likely to:
- Continue DDoS-focused operations through 2026, with possible spikes around political or geopolitical events (e.g. Algeria–Morocco, Gaza, India-region operations)
- Maintain broad targeting across government, technology, and financial sectors in Middle East, North Africa, Europe, and South Asia
- Rely on Telegram and X for coordination, recruitment, and proof-of-impact; monitoring of relevant channels and DDoS-for-hire (e.g. EliteStress) remains valuable for early warning
- Deepen or shift partnerships with other hacktivist and DDoS actors (e.g. DDoS54, NoName057(16), Mr Hamza), increasing potential for large-scale collaborative attacks
- Occasionally mix in data breach/leak claims alongside DDoS for added pressure and visibility
Defenders in Morocco, France, India, Egypt, Israel, UAE, and Pakistan and in government, technology, and financial services should treat Keymous+ as a high-risk disruption actor and prioritize DDoS resilience, visibility, and threat intelligence that includes Telegram and open-web activity.
Conclusion
Keymous+ has established itself as a high-volume, DDoS-specialist hacktivist collective with over 1,400 incidents tracked by DarkWebSonar and activity extending into early 2026. Attributed to Algeria (medium confidence) and linked to Algeria–Morocco tensions and pro-Palestine hacktivist circles, the group combines ideologically motivated targeting with DDoS-for-hire (EliteStress) and partnerships with actors such as DDoS54 and NoName057(16). Their focus on government, technology, and financial sectors across Morocco, France, India, Egypt, Israel, and beyond makes them a persistent disruption threat for organizations in those areas.
Understanding their tactics—including reflection/amplification, multivector floods, and collaborative operations—alongside Telegram- and X-driven coordination helps security teams prioritize DDoS resilience and leverage continuous dark web and Telegram monitoring to stay ahead of campaigns.
Dark Web Most Wanted profiles are powered by DarkWebSonar's continuous monitoring of threat actors across dark web forums, leak sites, and Telegram ecosystems.