
- Name: DimasHxR
- Type: Web Defacement Specialist
- First Seen (DarkWebSonar): November 2025
- Last Seen: May 2026
- Primary Activity: Website Defacement (100% of tracked incidents)
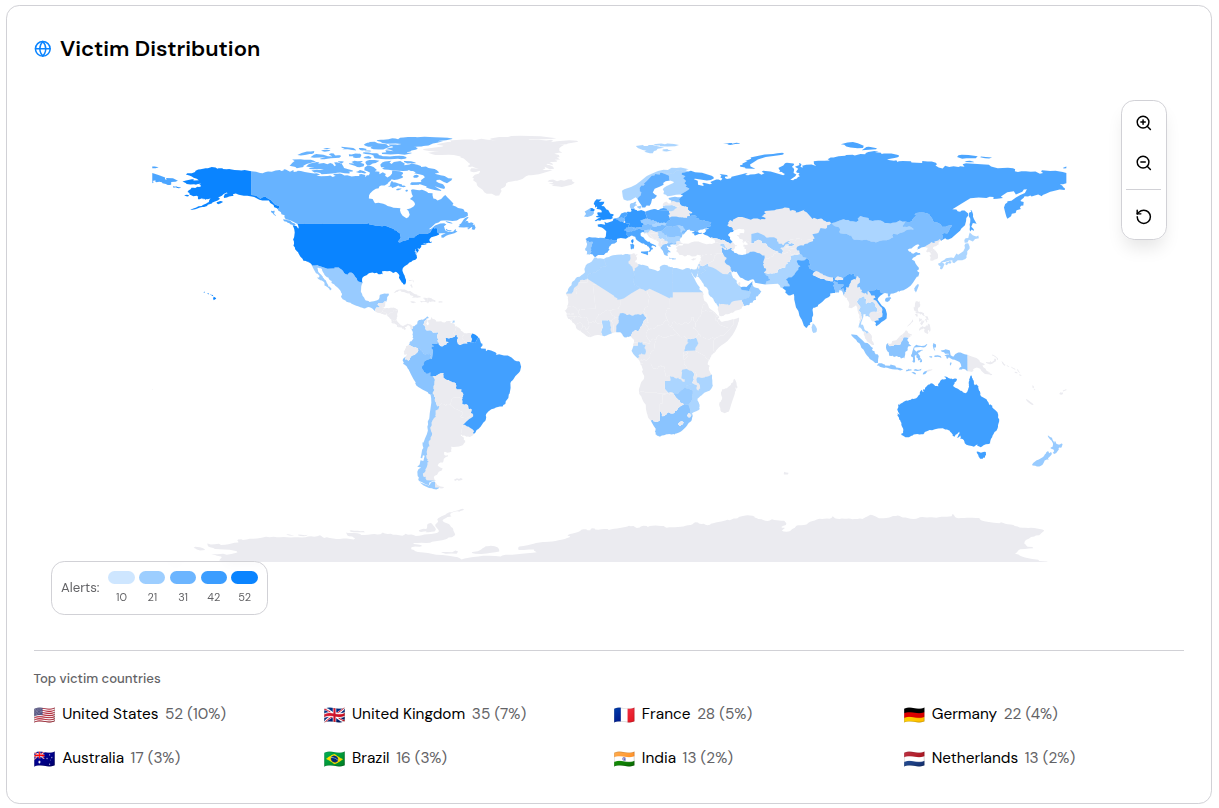
- Primary Region: Global — 74 victim countries
- Risk Level: High
Executive Summary
In just over five months, DimasHxR has gone from unknown to one of the most active web defacement actors in DarkWebSonar's global feed. With 508 incidents in the last 90 days, the actor ranks second only to NoName057(16) across all tracked threat actors in that window, yet unlike NoName, at the time of writing, DimasHxR carries zero open-source footprint. No public blog posts, no industry advisories, no attribution reports. The actor exists almost entirely in defacement mirror archives.
The headline numbers are striking: 523 total incidents since first appearing on 26 November 2025, a +3,287% jump in volume compared with the prior 90-day period, and a single-day peak of 55 incidents on 16 April 2026. The actor's entire known portfolio is website defacement (MITRE T1491 / T1491.002) with no ransomware, no DDoS, and no data exfiltration observed. What makes DimasHxR notable is not sophistication but scale and speed: broad, indiscriminate targeting across 74 countries, with retail, technology, and healthcare websites bearing the brunt, and a demonstrated willingness to return to already-hit properties.
Importantly, our weekly telemetry now shows three consecutive weeks of declining volume following the April 7–13 peak, suggesting the initial surge may be decelerating, whether due to target saturation, a patched vulnerability class, or a change in operational tempo remains to be seen.
By the Numbers (DarkWebSonar Telemetry)
- Total incidents tracked (Nov 2025 – May 2026): 523
- Incidents (last 90 days): 508
- Prior 90-day baseline (comparison window): 15
- Attack type concentration: Defacement — 100% of all tracked incidents
- Primary channel: Clear web defacement archives (523 / 523 incidents)
- Activity classification (DarkWebSonar): Spiked
- Victim countries: 74
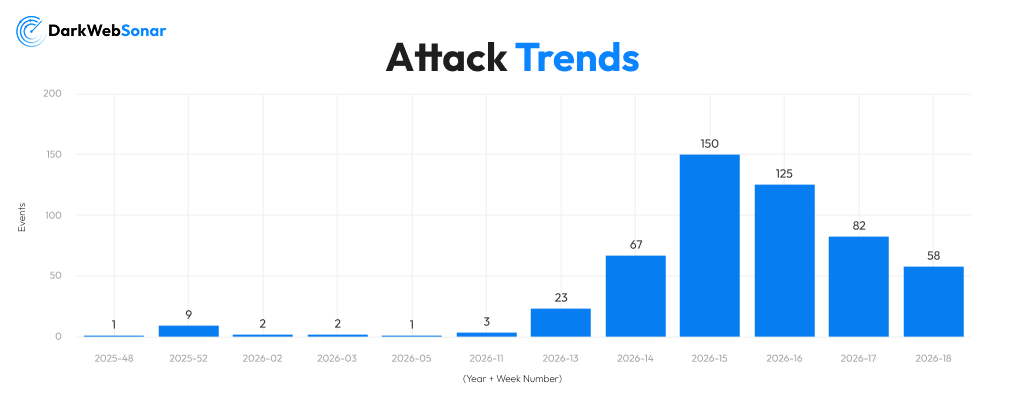
The April 2026 surge defines DimasHxR's profile, but so does what came after. After a quiet debut in late November 2025 and minimal activity through early 2026, the actor escalated sharply beginning the week of 23 March (W2026-13: 23 incidents), then accelerated further into April:
| ISO Week | Dates | Incidents |
|---|---|---|
| 2026-W13 | Mar 23–29 | 23 |
| 2026-W14 | Mar 30 – Apr 5 | 67 |
| 2026-W15 | Apr 6–12 | 150 (peak) |
| 2026-W16 | Apr 13–19 | 125 |
| 2026-W17 | Apr 20–26 | 82 |
| 2026-W18 | Apr 27 – May 3 | 58 |
Activity peaked in week 15 (April 6–12) and has since declined for three consecutive weeks: 125, then 82, then 58 (61% drop from peak). Whether this reflects target saturation, a closed vulnerability, or a deliberate pause is not yet established; the actor last appeared in DarkWebSonar on 1 May 2026.
Targeting Profile
Top Targeted Countries
DimasHxR's targeting is geographically broad with a Western tilt. In the last 90 days, where country attribution is available, five countries account for the largest share of attributed incidents:
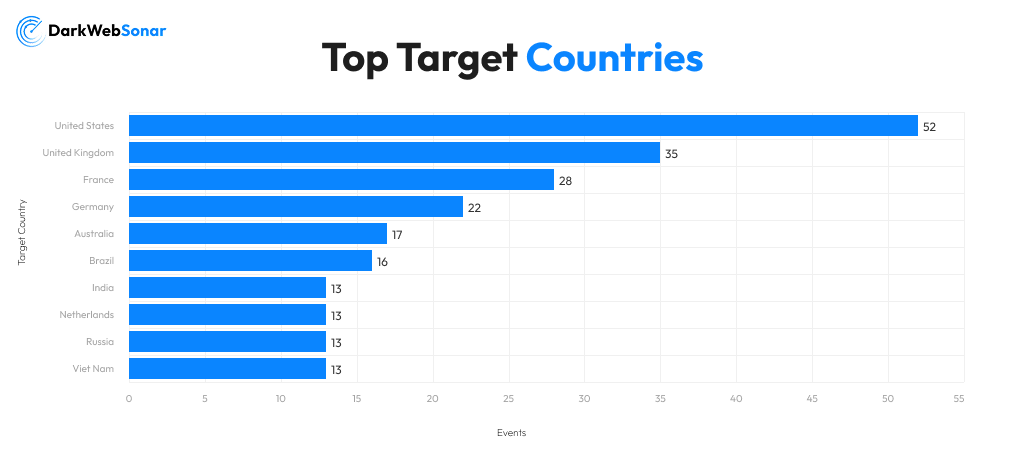
A second tier follows closely: Brazil (16 incidents lifetime), India, Netherlands, Viet Nam, Russia, Italy, and Poland each in the 12–13 range. At the outer edge, incidents span an additional ~60 countries (from Barbados and Gabon to Zimbabwe and Mongolia) confirming that targeting is opportunistic rather than geopolitical, driven by internet-exposed vulnerabilities rather than country-specific ideology.
Top Targeted Industries
Retail & E-commerce is the dominant sector by a wide margin: 160 incidents lifetime (~31% of total), with 159 of those occurring in the last 90 days, essentially all retail targeting is a product of the recent surge. The 90-day industry breakdown shows broad coverage across nine sectors:
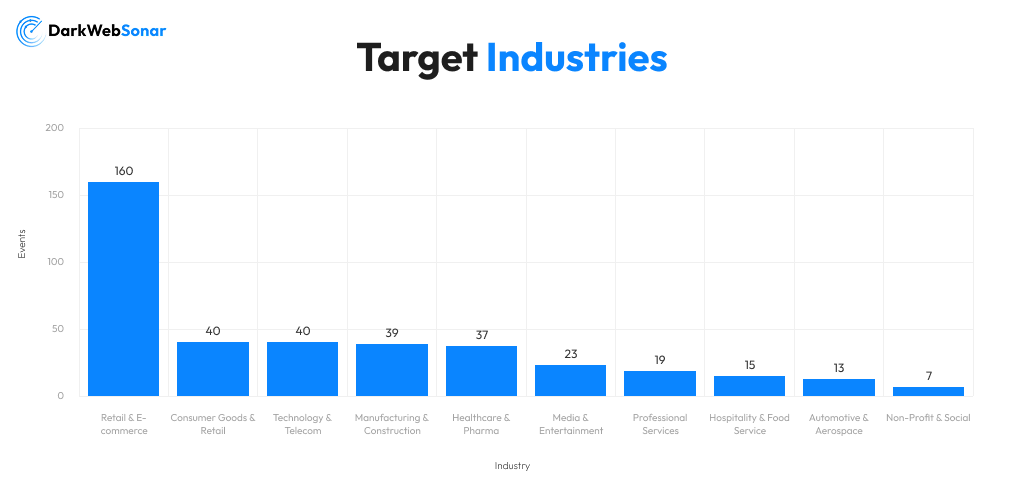
Nine distinct sectors in 90 days underscores an opportunistic strategy: DimasHxR is not sector-hunting but web-application hunting, sweeping exposed CMS instances, retail storefronts, and hosting platforms indiscriminately.
Attack Profile & Tactics
Here our telemetry paints a clean tactical picture for DimasHxR. Every tracked incident maps to website defacement, no secondary activity categories (ransomware, DDoS, data breach, initial access) appear at all in the actor's profile.
Core technique: External Web Defacement — MITRE T1491 / T1491.002. The enriched profile maps 523 incidents to these two techniques, consistent with the parent/child relationship between T1491 and T1491.002.
Observed execution patterns (from DarkWebSonar entries):
- Subpage and file-level targeting: Several incidents involve modifying specific files (e.g. 'b.html', 'd.txt', 'readme.txt') rather than root content, suggesting access via directory traversal, file upload vulnerabilities, or CMS plugin flaws rather than full administrative takeover
- Redefacement behavior: At least one confirmed case (Adidas Shoes Colombia, 'adidas-shoes.com.co') shows the actor returning to a previously compromised property, indicating persistent access or an unpatched vulnerability rather than one-shot exploitation
- Target breadth: Incidents span ISPs (Brazil), global retail brands (Colombia), media platforms (Indonesia), regional hosting (Russia), and e-commerce shops, no single platform or CMS type dominates, consistent with automated scanning and mass exploitation
- Proof of compromise: All incidents surface on public defacement mirror archives on the open web, consistent with visibility-oriented tradecraft — the goal is publication of the defacement, not quiet persistence
- Severity scores: Individual entries score in the mid range (~5.0–5.7) on DarkWebSonar's scale, reflecting the limited direct data impact of defacement versus ransomware or exfiltration; however, brand and availability impact can be significant
No tools, CVEs, or specific exploits are attributed to DimasHxR in current data, and no open-source research (as of May 2026) provides any technical reporting on the actor's infrastructure or toolchain.
Origins & Motivation
DimasHxR is, as of this writing, entirely undocumented in public threat intelligence. Searches across industry reporting, defacement community forums, and threat intel blogs return no attribution, no country-of-origin claim, and no stated motivation for this actor.
What DarkWebSonar telemetry does establish is a clear behavioral arc with a defined peak and a subsequent decline:
- Debut (Nov 2025 – Feb 2026): 15 total incidents across scattered dates, effectively dormant
- Escalation (W2026-13, Mar 23–29): 23 incidents mark the start of a significant uptick
- Acceleration (W2026-14, Mar 30 – Apr 5): 67 incidents; the actor crosses into high-volume territory
- Peak (W2026-15, Apr 6–12): 150 incidents — the busiest week, with single-day highs of 51 (Apr 9) and no day below 5
- Decline (W2026-16 to W2026-18): 125 → 82 → 58, three successive weekly drops totalling a 61% reduction from peak
The acceleration from near-zero to 150 incidents in a week is not consistent with purely manual operation. The most probable explanation is automated exploitation of a common vulnerability class (CMS misconfigurations, default credentials, or a shared hosting panel weakness) that DimasHxR began weaponizing at scale in late March 2026. The subsequent deceleration may reflect target pool exhaustion within that vulnerability class, defensive patching across affected hosts, or a deliberate operational pause. No geopolitical trigger has been identified to explain either the timing of the surge or the slowdown.
Possible motivations, in order of plausibility:
- Notoriety and ranking — Defacement actors commonly pursue placement on defacement archive leaderboards; volume is the metric
- Practice or training — High volume, low sophistication, and low persistence are consistent with skill-building
- Hacktivist signaling — Cannot be excluded; defacement pages may carry political content not captured in DarkWebSonar summaries
- Commissioned activity — Less likely given the absence of any known marketplace presence
Notable Campaigns

Five recent DarkWebSonar entries illustrate the scope and tactics:
- Net Infinito — Brazil (May 2026): Subpage compromise on 'netinfinito.com.br', a Brazilian internet service provider. File-level intrusion ('b.html') rather than homepage takeover, suggesting a vulnerability in a specific application path.
- Adidas Shoes Colombia — Colombia (April 2026): Described by DarkWebSonar as a redefacement, meaning 'adidas-shoes.com.co' had been compromised by this actor before. Persistent access or an unpatched weakness allowing repeated exploitation.
- Lyfecrush — Russia (April 2026): Defacement of 'lyfecrush.ru' with no disclosed motive or affiliation. Consistent with opportunistic targeting of internet-facing sites on shared hosting.
- Dibbobitan — April 2026: 'readme.txt' modification on 'dibbobitan.shop', file-level access consistent with CMS upload directory exposure or FTP/SFTP credential compromise.
- CinemaIndo — Indonesia (April 2026): File path intrusion ('d.txt') on 'cinemaindo.org', a media streaming platform. Demonstrates reach into Asia-Pacific beyond the Western-heavy country volume.
Different continents, different industries, different attack paths, all resolving to the same actor. This is the hallmark of automated mass defacement, not targeted intrusion.
DarkWebSonar Insights
DarkWebSonar's continuous monitoring provides several observations that distinguish DimasHxR from other high-volume actors:
- Second-highest 90-day volume across all tracked actors: 508 incidents, trailing only NoName057(16) (693), yet DimasHxR operates with zero open-source coverage, making DarkWebSonar the only real-time visibility source for this threat
- Fastest recent acceleration on record: +3,287% increase from prior 90 days, among the largest momentum shifts observed in DarkWebSonar's active actor set
- Clear peak-and-decline pattern: After hitting a single-week high of 150 incidents (W2026-W15), the actor has posted three consecutive weeks of declining volume (125, 82, 58) suggesting the surge phase may be ending
- Pure defacement specialization: No multi-vector behavior; all 523 incidents map to a single MITRE technique pair (T1491 / T1491.002)
- Retail-first in the surge: 159 of 160 lifetime Retail & E-commerce incidents occurred in the last 90 days — a near-complete pivot into this sector during the peak
- Redefacement confirmed: At least one documented return to a previously hit property, elevating risk for organizations that perform cosmetic-only cleanup without root cause remediation
- No public attribution: As of May 2026, no industry or government source has published analysis of DimasHxR; DarkWebSonar monitoring is the earliest warning available
Defender Outlook (2026)
DimasHxR's trajectory presents a nuanced picture: a dramatic surge followed by a measured but consistent decline. The immediate threat level may be lower than at the April peak, but several risk factors persist:
- Residual activity remains elevated — 58 incidents in week 18 is still meaningfully higher than the pre-surge baseline of ~2–3 incidents per week; a return to high tempo cannot be ruled out if a new vulnerability class is targeted
- Retail and e-commerce properties remain at the highest risk — 31% of lifetime incidents land in this sector; CMS patch cadence and WAF coverage should be treated as standing controls, not reactive responses to an active campaign
- Return visits to previously hit targets are confirmed — cleanup without root-cause remediation only delays the next compromise; treat every defacement as a sign of persistent access until proven otherwise
- The deceleration pattern warrants monitoring, not dismissal — if DimasHxR has exhausted one exploitable vulnerability class, a pivot to a new technique or platform could reset the volume counter quickly
- No geographic safe harbor — 74-country victim geography means this actor cannot be scoped out by region; any internet-exposed web application is potentially in scope
Technical controls to prioritize:
- Web Application Firewall (WAF) coverage for CMS file upload and admin paths
- File integrity monitoring on public web roots and critical content directories
- MFA enforcement on CMS admin panels, hosting control panels, and FTP/SFTP accounts
- Automated defacement detection via external URL monitoring or defacement archive feeds
- Dependency and plugin auditing on CMS-based properties, particularly those on shared hosting
Conclusion
DimasHxR is the defining example of a high-volume, low-profile defacement actor in 2026: over 500 incidents in five months, second-place 90-day activity across DarkWebSonar's global feed, and not a single line of open-source coverage. The April surge (peaking at 150 incidents in a single week) was striking; equally notable is the three-week decline that followed, suggesting a campaign lifecycle rather than indefinitely sustained tempo.
The core risk remains: retail storefronts, technology platforms, and healthcare web properties bear the heaviest exposure, the confirmed redefacement pattern means cleanup without remediation only delays the next hit, and a resumption to high volume is plausible at any point. For security teams, DimasHxR is a reminder that the most active threats are not always the most discussed ones — and that external surface monitoring, defacement archive feeds, and root-cause remediation discipline are the earliest and most reliable defenses against an actor the broader threat intelligence community has yet to document.
Dark Web Most Wanted profiles are powered by DarkWebSonar's continuous monitoring of threat actors across dark web forums, leak sites, and Telegram ecosystems.