
- Name: Sinobi
- Type: Ransomware Group
- First Seen: July 2025
- Last Seen: October 2025
- Risk Level: High
Introduction
Emerging in mid-2025, Sinobi has quickly positioned itself as one of the most aggressive ransomware operations tracked by DarkWebSonar.
Initially believed to be a rebrand of Lynx ransomware, Sinobi distinguishes itself through a high volume of U.S.-centric attacks targeting critical sectors such as healthcare, construction, and manufacturing.
After an early surge in August and a brief cooldown in September, Sinobi has resurged sharply in October 2025, signaling renewed affiliate activity and sustained operational capability.
By the Numbers (DarkWebSonar Data)
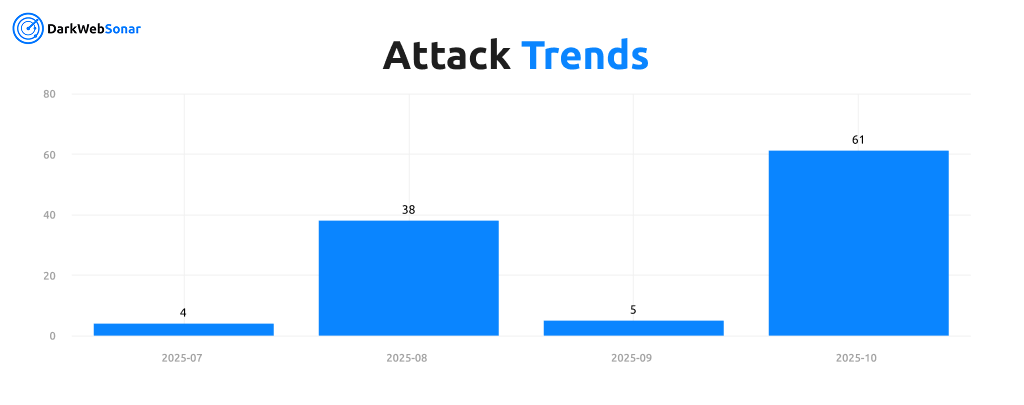
The timeline reveals a clear rebound in October, consistent with affiliate-driven RaaS (Ransomware-as-a-Service) campaigns that pause for retooling before major redeployments.
Attack Type Distribution
DarkWebSonar data confirms Sinobi’s exclusive focus on ransomware operations (100%), no evidence of DDoS or data breach claims has been observed.
This specialization allows affiliates to optimize encryption and exfiltration processes, emphasizing rapid compromise, exfiltration, and double extortion tactics to maximize pressure on victims.
Target Industries
Sinobi’s victim list showcases a deliberate focus on industries with critical uptime requirements, where disruption translates directly into leverage.
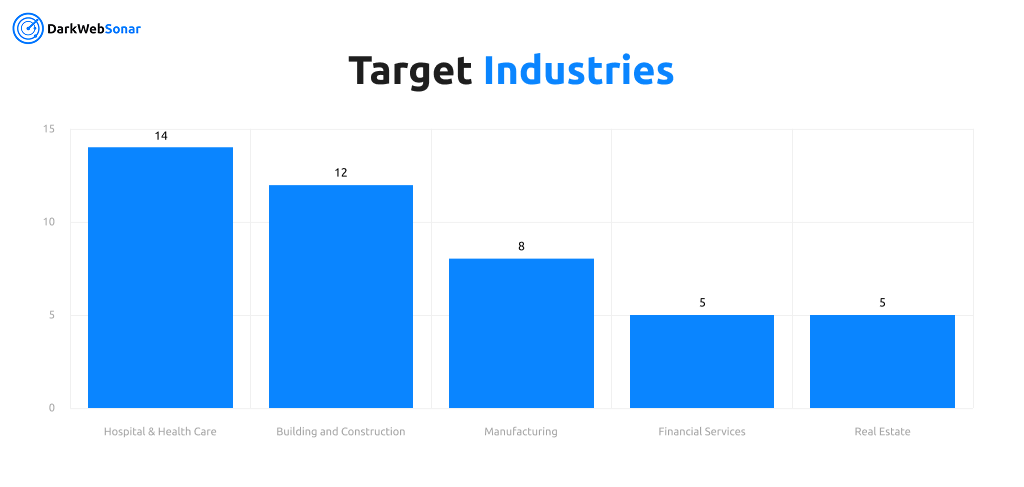
These findings align with independent assessments by Surefire Cyber which identified Sinobi as a major threat to U.S. industrial and healthcare sectors.
The heavy targeting of construction and healthcare reflects both supply-chain vulnerabilities and low tolerance for downtime, making them prime candidates for extortion.
Top Targeted Countries (2025)
Sinobi’s geographic footprint is dominated by U.S. victims, accounting for more than 85% of all known incidents.
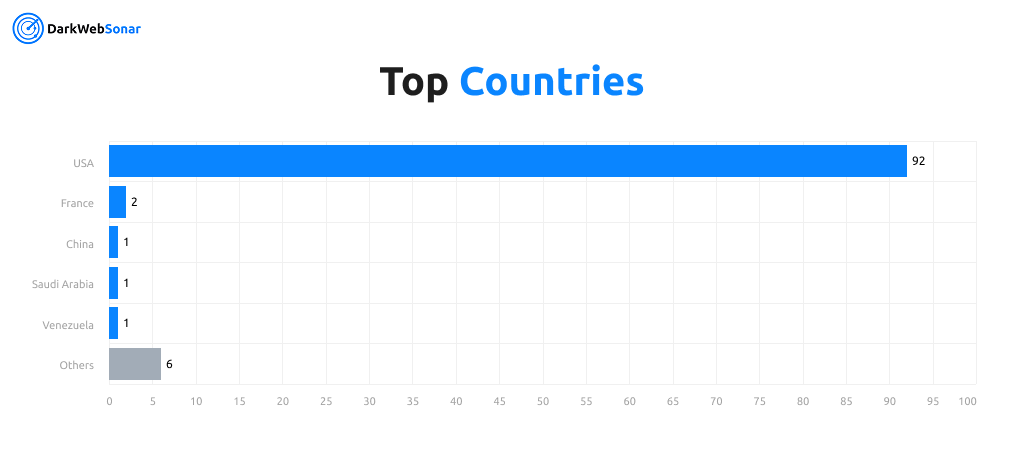
Beyond the U.S., a handful of victims in France, Taiwan, and Saudi Arabia point to opportunistic attacks by individual affiliates rather than coordinated global expansion.
This U.S.-heavy concentration mirrors reporting from CYFIRMA and eSentire, who attribute many of these compromises to exploited SonicWall SSL-VPN credentials.
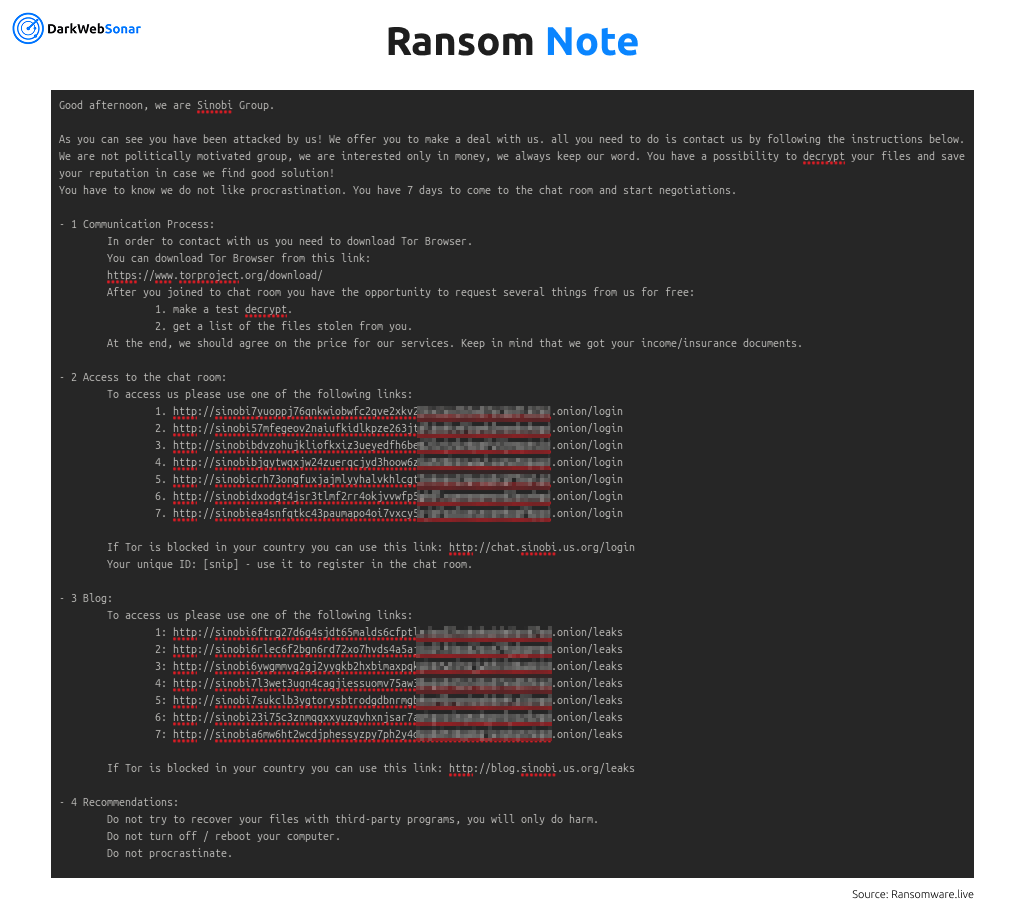
Tactics, Techniques & Procedures (TTPs)
Sinobi leverages compromised VPN credentials and unpatched SonicWall devices (CVE-2024-40766) as its primary entry vector.
Once inside, affiliates create local administrator accounts, disable EDR tools such as VMware Carbon Black, and deploy ransomware payloads using AES-128-CTR encryption with .SINOBI file extensions.
The group follows a double-extortion model, combining encryption with data exfiltration using tools like RClone for cloud transfers. Victims are then pressured through Tor-based negotiation portals and leak site postings.
DarkWebSonar Insights
DarkWebSonar’s continuous monitoring highlights Sinobi’s operational maturity and rapid adaptability:
- Rebound in activity: 61 confirmed incidents in October after a September slowdown.
- Infrastructure reuse: Strong overlap with Lynx ransomware panels and leak site design.
- U.S. focus: 92 confirmed American victims since July.
- Exploit-driven access: Correlation with SonicWall VPN exploit waves in Q3–Q4 2025.
- Affiliate expansion: Surge in ransom postings indicates renewed recruitment and coordination.
Sinobi’s evolution underscores how modern ransomware operations operate as fluid ecosystems by rebranding, franchising, and adapting tooling as defensive measures evolve.
Outlook
Sinobi’s October resurgence suggests it is transitioning from an emerging threat to a sustained ransomware enterprise.
Its consistent targeting of critical infrastructure sectors, combined with rapid affiliate onboarding, mirrors the growth trajectories of established groups like Akira and Qilin earlier this year.
While its activity remains heavily U.S.-focused, the group’s increasing visibility and technical overlap with prior ransomware families indicate long-term persistence and potential for further expansion.
Conclusion
Sinobi exemplifies the modern RaaS lifecycle with rapid emergence, brief dormancy, and aggressive reactivation. Its precision targeting of vulnerable sectors demonstrates a high degree of operational coordination and affiliate discipline.
For defenders, this reinforces the importance of:
- Patching exposed VPN infrastructure
- Monitoring for credential reuse and RClone activity
- Maintaining segmented networks and immutable backups
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar’s continuous monitoring of ransomware leak sites and underground ecosystems.
For real-time visibility into groups like Sinobi, contact our team.