
- Name: Qilin
- Type: Ransomware Group
- First Seen: Oct 2024
- Last Seen: Aug 2025
- Risk Level: High
Introduction
Qilin has rapidly risen to become one of the most active ransomware groups in 2025. With 442 confirmed victim posts tracked by DarkWebSonar this year, the group tops our list of Dark Web Most Wanted actors. Known for aggressive targeting across multiple industries, Qilin exemplifies how leak sites are being weaponized to pressure victims into paying ransoms.
By the Numbers (DarkWebSonar Data)
- Victim posts (2025 YTD): 442
- Rank: #1 most active group
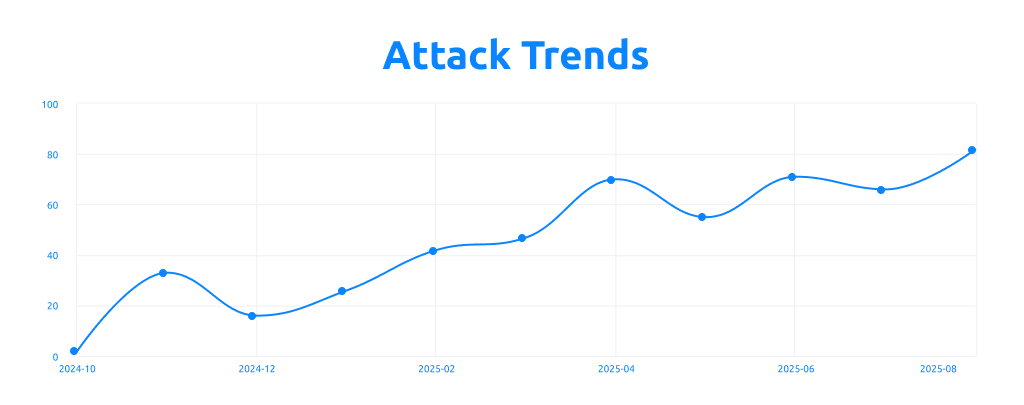
- Activity trend: Significant surge in Q2 2025
- Top targeted industries:
- Building & Construction – 28 victims
- Manufacturing – 23 victims
- Healthcare – 21 victims
- Automotive – 21 victims
- Financial Services – 17 victims
- Geographies: Predominantly U.S. and Europe, but with victims across multiple regions.
Tactics, Techniques & Procedures (TTPs)
Extortion Strategy
- Double extortion: Combines data encryption with data theft and leak threats
- Escalation tactics: Progresses from private negotiations to public data releases
- Leak site behavior: Publishes victim names, company logos, and sample files with to maximize pressure
Initial Access Methods
- Spear phishing campaigns: Deploys malicious attachments targeting specific organizations
- Compromised credentials: Exploits stolen VPN credentials and Remote Desktop Protocol (RDP) access
- Supply chain attacks: Targets Managed Service Providers (MSPs) to gain access to multiple downstream victims
- Vulnerability exploitation: Recent campaigns heavily focused on Fortinet vulnerability exploitation (CVE-2024-21762 and CVE-2024-55591)
Technical Capabilities
- Cross-platform ransomware: Deploys variants targeting Windows, Linux, and VMware ESXi environments
- Multi-language development: Written in both Go and Rust programming languages for enhanced performance
- Customizable encryption: Features configurable encryption modes and advanced evasion techniques
- Automated exploitation: Provides affiliates with automated tools for vulnerability exploitation
Business Model & Operations
- Ransomware-as-a-Service (RaaS): Operates affiliate program with 80-85% commission structure
- Legal support services: Recently introduced "Call Lawyer" feature providing affiliates with legal guidance
- Targeting approach: Wide, cross-sector focus with opportunistic methodology based on exploitable vulnerabilities
Notable Campaigns / Victims
- Multiple high-profile victims across manufacturing and healthcare sectors
- Known to target supply chain partners, amplifying downstream impact
- Recent major attack: Nissan confirmed breach exposing 4TB of design data (August 2025)
- Aggressive posting style: uses branding and public threats to pressure negotiations
- Data validation tactics: Publishes sensitive executive information (driving licenses, salary details) as proof of compromise
Evolution & Trends
- Emergence: Gained momentum in 2024, but saw explosive growth in 2025
- Trend: 80% activity surge in Q2 2025 compared to Q1
- Trajectory: While some groups consolidated or went offline, Qilin expanded its footprint and visibility
- Technical evolution: Continuous development of cross-platform capabilities and evasion techniques
- Operational maturity: Enhanced affiliate support systems and legal advisory services
DarkWebSonar Insights
Unlike traditional reports that summarize ransomware activity quarterly, DarkWebSonar tracks victim postings in real time. This allows us to identify:
- Qilin's precise industry targeting patterns (construction, manufacturing, healthcare)
- Rapid shifts in activity, including their Q2 surge while other groups declined
- Early warning when victims are named on their leak site, often before public disclosure
- Exploitation campaign timing: Real-time correlation between vulnerability disclosures and Qilin attack waves
- Affiliate recruitment patterns: Monitoring of RaaS program expansion and commission structure changes
Threat Intelligence Indicators
Key Vulnerabilities Exploited
- CVE-2024-21762: Fortinet out-of-bounds write vulnerability enabling remote code execution
- CVE-2024-55591: Fortinet authentication bypass vulnerability for privilege escalation
Attack Progression Timeline
- Initial compromise through phishing, credential theft, or vulnerability exploitation
- Lateral movement and privilege escalation within target networks
- Data exfiltration prior to encryption deployment
- Ransomware deployment across Windows, Linux, and ESXi systems
- Extortion initiation with leak site posting and negotiation demands
Outlook
Qilin shows no sign of slowing down. With consistent targeting of critical sectors and adoption of advanced exploitation tactics, the group is expected to remain a top ransomware threat into late 2025. Their diversified victim pool suggests they are opportunistic but capable of focusing on industries most likely to pay. The group's recent technical innovations and enhanced affiliate support systems indicate continued operational sophistication and expansion.
Conclusion
Qilin exemplifies how ransomware groups use the dark web as a weapon of pressure. By naming and shaming victims on leak sites, they turn operational compromise into reputational and regulatory leverage. The group's evolution from a traditional ransomware operation to a sophisticated RaaS platform with comprehensive affiliate support demonstrates the maturation of cybercriminal enterprises in 2025.
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar's continuous monitoring of ransomware leak sites. Want real-time visibility into groups like Qilin? Contact Sales.