
- Name: NOTCTBER404
- Type: Hacktivist Collective
- First Seen: August 2025
- Last Seen: October 2025
- Risk Level: Medium–High
Introduction
Emerging suddenly in August 2025, NOTCTBER404 has become one of the fastest-growing hacktivist collectives tracked by DarkWebSonar.
In less than two months, the group’s DDoS campaigns surged from isolated claims to over 100 verified incidents, primarily targeting government and education institutions across Southeast Asia.
Their operational tempo and recent alliance with HEZI RASH mark NOTCTBER404 as a rising force in the region’s hacktivist ecosystem, one blending ideological messaging with digital disruption.
By the Numbers (DarkWebSonar Data)
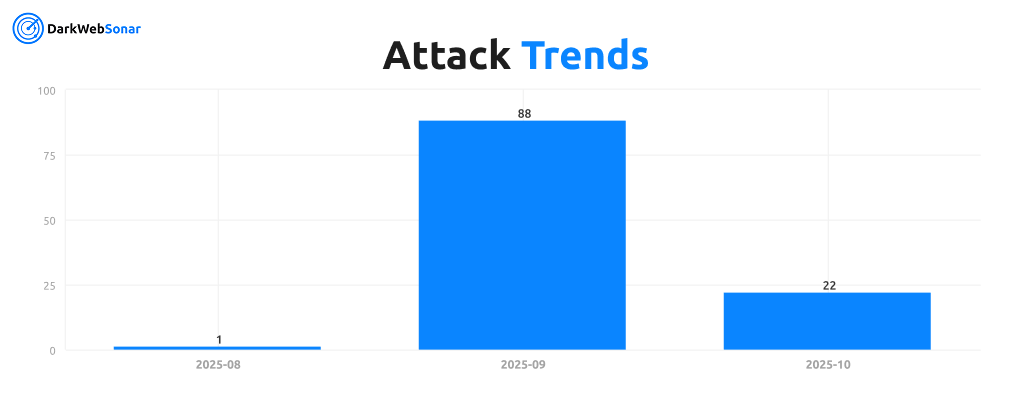
- Total incidents (2025 YTD): 110
- Aug 2025 — 1 post (first appearance)
- Sep 2025 — 88 posts (initial campaign surge)
- Oct 2025 — 22 posts (sustained activity)
Attack Type Distribution
DarkWebSonar data shows that over 96% of NOTCTBER404’s operations involve DDoS attacks, signaling a strategy focused on visibility and disruption rather than infiltration or data theft.
While a handful of data-breach and access claims exist, they appear opportunistic, intended to amplify propaganda or test capability expansion.
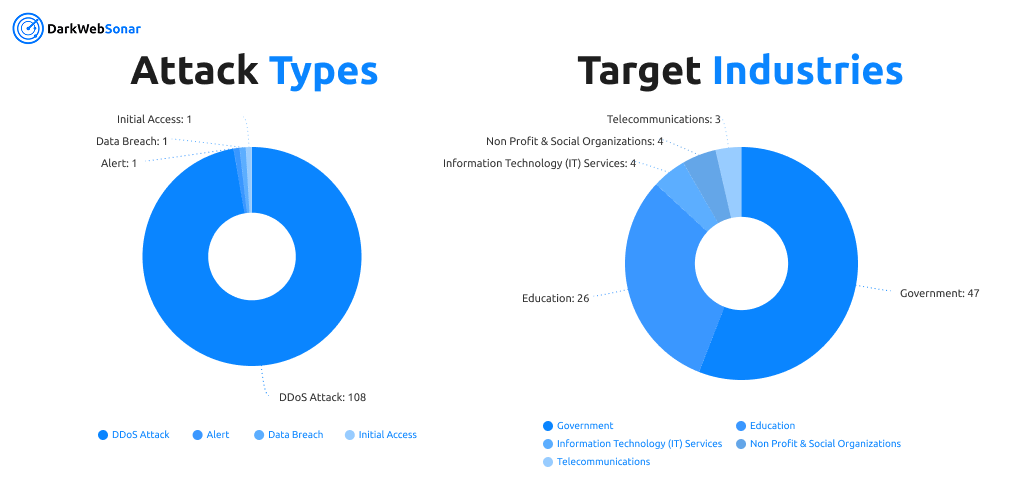
The group’s targeting reflects a symbolic and politically aligned focus. Government and educational sectors dominate their victim list, suggesting an intent to disrupt public-facing institutions and information channels rather than pursue profit.
Top Targeted Countries (2025)
The geographic footprint of NOTCTBER404’s campaigns is strikingly regional.
Thailand accounts for nearly 80% of observed attacks, making it both the epicenter and likely staging ground of operations.
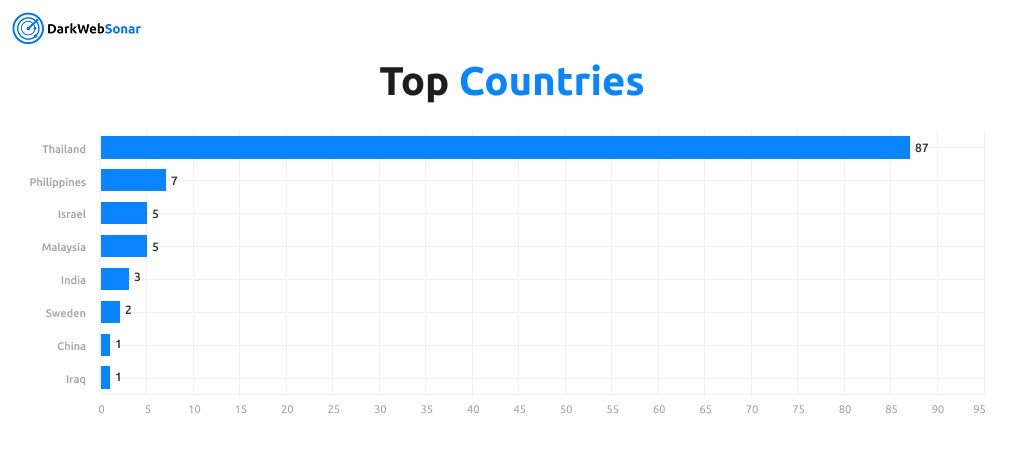
Secondary targeting across the Philippines, Malaysia, and India suggests a widening Southeast Asian agenda. Beyond Southeast Asia, a handful of incidents involving Israel and Sweden hint at opportunistic collaborations with ideologically aligned actors such as HEZI RASH.
Alliances and Collaboration
In September 2025, NOTCTBER404 publicly announced an alliance with HEZI RASH, another rapidly expanding hacktivist entity.
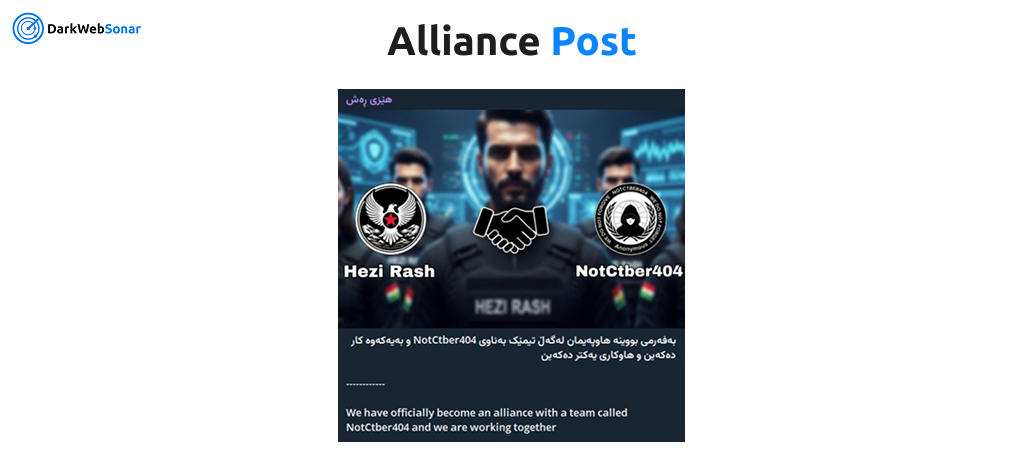
Joint operations observed on Telegram and underground forums indicate coordinated DDoS campaigns and shared propaganda materials.
This partnership mirrors trends seen among earlier hacktivist coalitions such as Anonymous Sudan and DarkStorm Team, where ideological alignment and brand amplification outweigh deep operational integration.
DarkWebSonar Insights
DarkWebSonar’s continuous monitoring of leak sites, forums, and Telegram channels provides a clear view of NOTCTBER404’s evolution:
- Rapid growth: From 1 post in August to 88 in September (a >10,000% spike in activity).
- Regional focus: Thailand-centric operations show a strong local narrative.
- Cross-group amplification: HEZI RASH mentions appear in nearly half of NOTCTBER404’s September posts.
- Low technical complexity: Predominantly Layer-7 DDoS attacks; no verified malware payloads detected.
- Media strategy: Uses “alert posts” and screenshots to showcase impact and attract attention on Telegram and X (Twitter).
This pattern reinforces that NOTCTBER404 is a propaganda-driven operation, relying on volume and coordination rather than novel exploits.
Outlook
NOTCTBER404 is poised to remain active through late 2025 as part of a broader Southeast Asian hacktivist surge.
Its partnership with HEZI RASH may lead to expanded targeting beyond the region, particularly against organizations perceived as politically symbolic or aligned with Western or Israeli interests. However, the group’s dependence on basic DDoS infrastructure and lack of technical depth suggest limited scalability without external support.
If their visibility continues to grow, it may attract alliances with more established collectives or law-enforcement scrutiny.
Conclusion
NOTCTBER404’s meteoric rise highlights how quickly new hacktivist brands can gain traction through social amplification and ideological messaging.
By combining quantity over complexity, and leveraging alliances to magnify reach, the group exemplifies the next generation of regional digital activism blending politics, propaganda, and cyber disruption.
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar’s continuous monitoring of dark-web and Telegram ecosystems.
For real-time visibility into emerging hacktivist collectives like NOTCTBER404, contact our team.