
- Name: MEDUSA
- Type: Ransomware Group
- First Seen: October 2024
- Last Seen: November 2025
- Risk Level: High
Introduction
MEDUSA has established itself as one of the most persistent and active ransomware groups of 2025, with 201 confirmed victim postings tracked by DarkWebSonar since October 2024. Operating as a ransomware-as-a-service (RaaS) platform, MEDUSA demonstrates sustained operational capability with a spiked activity pattern that indicates aggressive targeting campaigns and strong affiliate recruitment.
Known for their double extortion tactics and opportunistic targeting across multiple sectors, MEDUSA has maintained consistent operations throughout 2025, with activity extending through late November. The group's strong focus on U.S. enterprises—accounting for 61.7% of all observed victims—positions them as a critical threat to North American organizations, particularly in construction, education, and healthcare sectors.
By the Numbers (DarkWebSonar Data)
- Total incidents (Oct 2024–Nov 2025): 201
- First seen: October 7, 2024
- Last seen: November 29, 2025
- Activity level: Spiked – sustained high-volume operations with periodic surges
- Risk score (DarkWebSonar): 90 (High)
Attack type distribution:
MEDUSA's operations are exclusively ransomware-focused, with all 201 logged incidents involving ransomware deployments. This singular focus on encryption and data-leak extortion underscores their specialization as a dedicated ransomware operation, distinguishing them from hacktivist groups or mixed-operation actors.
The group operates through Tor-based leak sites (201 incidents), maintaining a traditional ransomware-as-a-service model where affiliates conduct attacks and MEDUSA provides infrastructure, negotiation support, and victim shaming through their public portal.
Top targeted countries (2024-2025):
MEDUSA demonstrates a strong North American and Western European focus, with the United States dominating their victim list at 124 incidents (61.7% of all observed cases). This heavy concentration on U.S. targets reflects the group's strategic targeting of organizations most likely to pay ransoms and where regulatory pressure creates additional leverage.
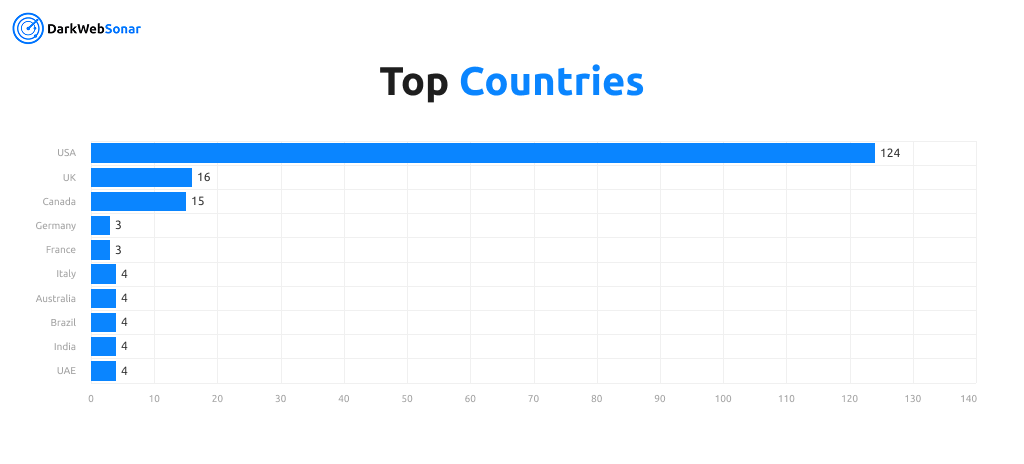
Beyond the U.S., MEDUSA maintains a global footprint with significant activity in:
- United Kingdom: 16 incidents (8.0%)
- Canada: 15 incidents (7.5%)
- Germany, France, Italy: 3–4 incidents each
- Australia, Brazil, India: 4 incidents each
The group has also targeted victims across 26 total countries, including nations in Asia-Pacific (Singapore, Malaysia, Thailand, Indonesia), Latin America (Chile, Dominican Republic, Peru), and the Middle East (UAE, Saudi Arabia). This geographic diversity suggests MEDUSA's affiliates operate globally while maintaining a core focus on high-value Western targets.
Top targeted industries:
MEDUSA shows diverse industry targeting with a particular emphasis on sectors that generate maximum pressure to pay ransoms. Building & Construction, Education, Hospital & Health Care.
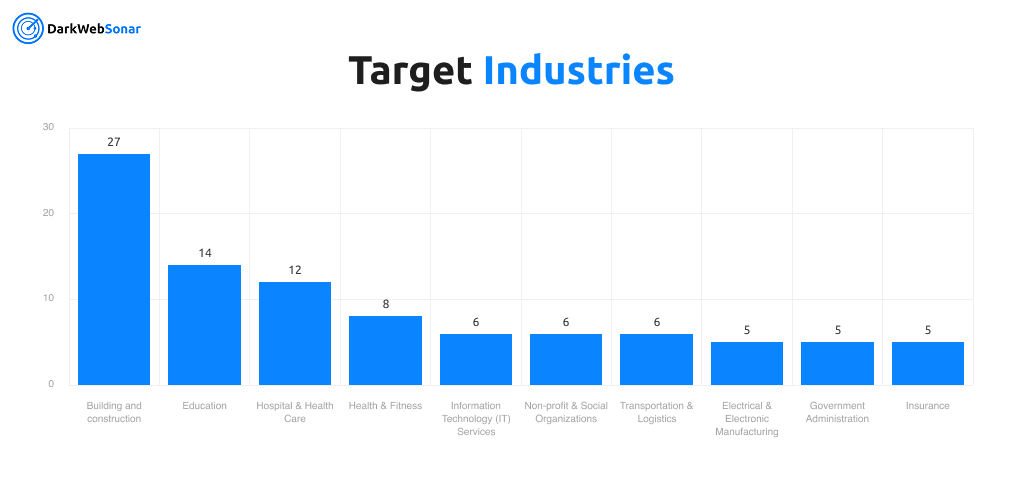
Notable sector distribution:
- Construction & Infrastructure: Building and construction (27), Civil Engineering (2)
- Healthcare: Hospital & Health Care (12), Pharmaceuticals (4), Medical Practice (4), Health & Fitness (8)
- Education: Education (16)
- Professional Services: Law Practice & Law Firms (3), Legal Services (2), Accounting (3)
- Manufacturing: Manufacturing & Industrial Products (7), Machinery Manufacturing (3)
- Financial Services: Financial Services (4), Insurance (5), Investment Management (1)
The emphasis on construction, healthcare, and education aligns with ransomware groups' strategic preference for industries where operational disruption creates immediate financial pressure, regulatory compliance concerns, and public safety implications that increase the likelihood of ransom payments.
Tactics, Techniques & Procedures (TTPs)
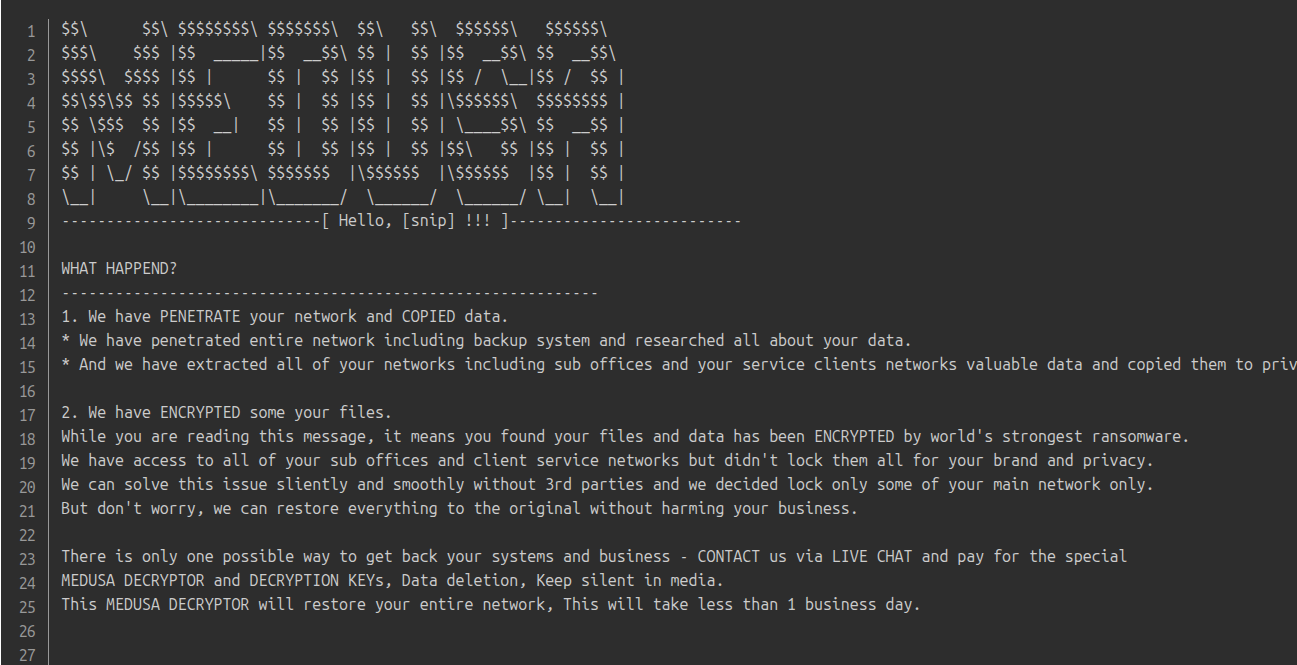
Extortion Strategy
- Double extortion: Encrypts files while exfiltrating sensitive data for additional leverage
- Leak site publishing: Victim details posted on Tor-based portals to pressure payments
- Negotiation tactics: Uses sample leaks of executive data and confidential files as proof of compromise
- Public shaming: Aggressive victim naming and data exposure to maximize reputational damage
Initial Access Methods
- Stolen credentials: Exploitation of compromised VPN credentials and Remote Desktop Protocol (RDP) access
- Phishing campaigns: Malicious attachments and credential stealers delivered via email
- Exploitation of vulnerabilities: Targeting known security flaws in enterprise software and network infrastructure
- Supply chain attacks: Potential targeting of managed service providers (MSPs) for downstream access
Technical Capabilities
- Cross-platform ransomware: Variants targeting Windows, Linux, and VMware ESXi environments
- Sophisticated encryption: Customizable encryption modes with selective file targeting
- Persistence mechanisms: Use of scheduled tasks, domain administrator compromise, and lateral movement tools
- Data exfiltration: Automated tools for stealing sensitive files prior to encryption
Business Model & Operations
- Ransomware-as-a-Service (RaaS): Affiliates earn commission-based share of ransoms
- Targeting approach: Opportunistic but skewed toward North American enterprises
- Branding: Maintains distinct Tor leak site with aggressive victim shaming
- Affiliate support: Provides negotiation assistance and technical infrastructure to operators
Notable Campaigns / Victims

MEDUSA's sustained operational tempo has produced numerous high-impact campaigns throughout 2024–2025:
- Construction sector targeting: 27 incidents against building and construction firms, reflecting the group's focus on industries where operational disruption creates immediate financial pressure
- Healthcare disruption: 20 total incidents across healthcare providers, hospitals, and pharmaceutical companies, targeting critical infrastructure where patient safety concerns amplify extortion leverage
- Education sector: 16 incidents against educational institutions, including universities and schools, where data privacy regulations create additional pressure points
- Professional services: Multiple high-profile breaches of law firms, accounting practices, and legal services, with sensitive client data leaked online
- Manufacturing operations: Sustained targeting of manufacturing and industrial companies, where production disruption generates immediate revenue loss
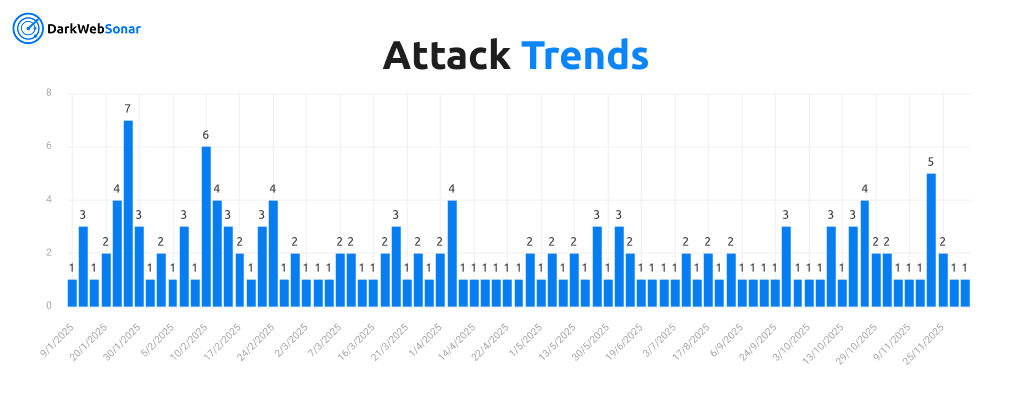
The group's spiked activity pattern shows clear campaign bursts, with notable surges in:
- January 2025: 27 incidents across multiple dates
- February 2025: 24 incidents with peak on February 10 (6 incidents)
- November 2025: 13 incidents, demonstrating continued operational capability
MEDUSA's Tor-based leak site enables rapid victim posting and negotiation pressure, with incidents often announced within days of compromise to maximize leverage during ransom negotiations.
Evolution & Trends
- Emergence: First observed October 7, 2024, with immediate operational activity
- Growth trajectory: Sustained operations throughout 2024–2025 with consistent monthly activity
- Activity pattern: Spiked activity level indicates coordinated bursts followed by consistent baseline operations
- Operational maturity: 108 distinct activity dates demonstrate organizational capacity for long-term campaigns
- Recent activity: Continued operations through November 2025, with 13 incidents in the final month of tracking
MEDUSA's spiked activity timeline shows clear operational patterns:
- Initial ramp-up: October–December 2024 established baseline operations
- Sustained campaigns: January–March 2025 represented peak activity period
- Consistent operations: April–November 2025 maintained steady victim posting despite potential law enforcement pressure
The group's ability to maintain consistent operations over 14 months while other ransomware groups experienced disruptions or takedowns demonstrates strong operational security, affiliate management, and infrastructure resilience.
DarkWebSonar Insights
Our telemetry reveals unique aspects of MEDUSA's operations:
- U.S. dominance: Over 61% of all known victims in our dataset are U.S.-based, reflecting strategic targeting of high-value Western enterprises
- Spiked activity pattern: Clear bursts of victim postings (e.g., February 10, 2025 with 6 incidents) suggest coordinated campaigns or batch leak site updates
- Industry targeting: Construction, education, and healthcare among top sectors, reflecting strategic selection of industries most likely to pay
- Affiliate-driven model: Activity patterns suggest multiple operators publishing under the MEDUSA brand, consistent with RaaS operations
- Operational persistence: 108 distinct activity dates over 14 months demonstrates sustained operational capability
Unlike static quarterly reports, DarkWebSonar provides real-time tracking of MEDUSA's victim postings, enabling early warnings before public disclosure. The group's spiked activity pattern allows for identification of campaign timing and affiliate coordination, providing valuable threat intelligence for organizations in targeted sectors.
The geographic concentration on North America (U.S. and Canada account for 69% of victims) creates specific risk profiles for organizations in these regions, while the diverse industry targeting ensures that multiple sectors remain at elevated risk.
Threat Intelligence Indicators
Attack Progression Timeline
- Initial compromise [TA0001] via stolen credentials, phishing, or vulnerability exploitation
- Lateral movement [TA0008] and privilege escalation across Windows, Linux, and ESXi systems
- Data exfiltration [TA0010] of sensitive files prior to encryption deployment
- Ransomware deployment [T1486] across servers and endpoints
- Leak site posting and ransom negotiation initiation
Operational Characteristics
- Tor-based infrastructure: All operations conducted through Tor leak sites for anonymity
- High-frequency operations: Capable of sustaining multiple incidents per day during peak periods
- Multi-continent reach: Infrastructure and targeting span North America, Europe, Asia-Pacific, and Latin America
- Symbolic targeting: Preference for construction, healthcare, and education sectors that generate public attention and regulatory pressure
Notable Geographic Patterns
- North American focus: USA (124 incidents, 61.7%), Canada (15 incidents, 7.5%)
- Western European targeting: UK (16 incidents), Germany (3), France (3), Italy (4)
- Global opportunism: Victims across 26 countries demonstrate worldwide affiliate network
Industry Risk Profile
Organizations in the following sectors face elevated risk:
- Construction & Building: 27 incidents (highest risk sector)
- Education: 16 incidents
- Healthcare: 20 total incidents across multiple healthcare subsectors
- Professional Services: Law firms, accounting, legal services
- Manufacturing: 10+ incidents across manufacturing subsectors
Outlook
MEDUSA shows no signs of operational decline as of November 2025. With 201 incidents logged over 14 months and sustained activity through late 2025, the group demonstrates the capacity for long-term disruptive campaigns.
Their RaaS model enables rapid scaling and coordination, while their focus on high-value Western targets (particularly U.S. enterprises) ensures continued financial motivation. The group's proven ability to maintain consistent operations despite potential law enforcement pressure positions them as a persistent threat for the remainder of 2025 and beyond.
Organizations in construction, healthcare, education, and professional services across North America remain at elevated risk, particularly during periods of spiked activity that suggest coordinated affiliate campaigns.
The group's spiked activity pattern, strong U.S. targeting, and diverse industry focus ensure that MEDUSA will remain a significant ransomware threat into 2026, with organizations in targeted sectors needing to maintain vigilant monitoring and robust security controls.
Conclusion
MEDUSA exemplifies how modern ransomware groups leverage RaaS platforms and double extortion tactics to achieve sustained operational impact. Their 201 incidents over 14 months, combined with a strong focus on U.S. enterprises and strategic industry targeting, underscores the evolving threat landscape where ransomware operations remain persistent risks to organizations globally.
With 61.7% of victims in the United States and emphasis on construction, healthcare, and education sectors, MEDUSA demonstrates the strategic targeting approach that maximizes both financial returns and operational disruption. The group's ability to maintain consistent operations while other ransomware groups experienced disruptions highlights the resilience of the RaaS model and the challenges facing law enforcement and security teams.
The spiked activity pattern observed in DarkWebSonar's telemetry provides valuable threat intelligence for organizations in targeted sectors, enabling early warning when campaign surges occur and allowing for enhanced defensive measures during high-risk periods.
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar's continuous monitoring of ransomware leak sites. Want real-time visibility into groups like MEDUSA? Contact Sales.