
- Name: HEZI RASH
- Type: Hacktivist Collective
- First Seen: July 2025
- Last Seen: November 2025
- Risk Level: High
Introduction
HEZI RASH has rapidly emerged as one of the most prolific hacktivist groups in the second half of 2025. With 856 total incidents tracked by DarkWebSonar in just over three months of activity, the group demonstrates an aggressive and sustained campaign targeting organizations across multiple continents.
Operating primarily through Telegram channels where they coordinate and announce attacks, HEZI RASH has established itself as a disruptive force focused on large-scale DDoS campaigns that account for more than 97% of their observed activity. The group's high-frequency operations and global targeting suggest a well-organized collective capable of sustained disruption campaigns.
By the Numbers (DarkWebSonar Data)
- Total incidents (July–Nov 2025): 856
- First seen: July 16, 2025
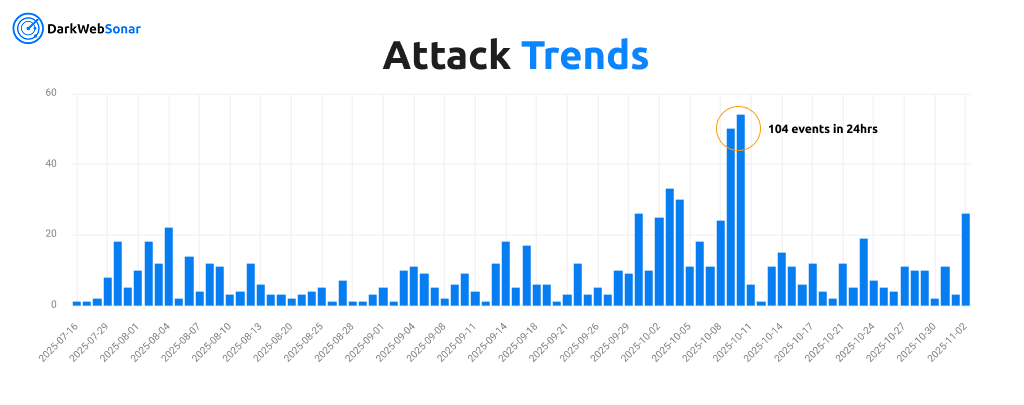
- Activity peak: October 9–10, 2025 (104 incidents in 24hrs)
- Activity level: Spiked – sustained high-volume operations
Attack type distribution:
HEZI RASH's operational profile is overwhelmingly dominated by DDoS attacks, which represent 834 of 856 logged incidents (97.4%). This near-exclusive focus on denial-of-service tactics positions the group as a disruption-oriented hacktivist collective rather than a financially motivated ransomware operation.
Top targeted countries (2025):
HEZI RASH demonstrates a highly distributed global footprint, with victims spanning 38 countries across Europe, Asia, the Middle East, and North America. Azerbaijan emerges as the top target with 167 incidents, followed closely by Turkey, Israel, Iran, and Japan.
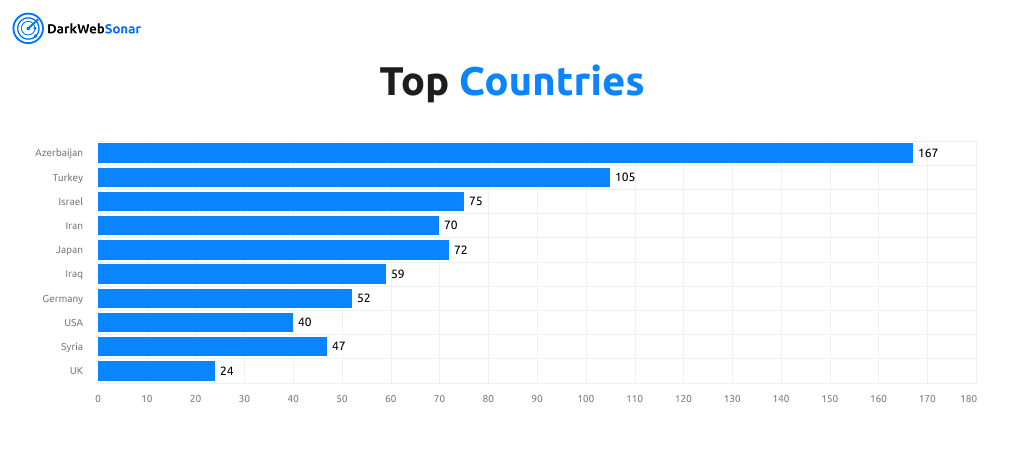
The group's targeting pattern reveals a complex geopolitical dimension with significant activity against:
- Middle Eastern nations: Azerbaijan, Turkey, Israel, Iran, Iraq, Syria
- Western countries: Germany, USA, UK, Canada
- Asian nations: Japan, Pakistan, Thailand
This geographic distribution suggests HEZI RASH operates with both ideological motivations and opportunistic targeting, striking symbolic targets while maintaining a broad operational scope that ensures maximum visibility and disruption impact.
Top targeted industries:
HEZI RASH shows diverse industry targeting, with Education, Broadcast, Government Administration, Political Organizations, and Healthcare among the most frequent victims. This pattern reflects a strategy of targeting critical infrastructure sectors that generate maximum public attention when disrupted.
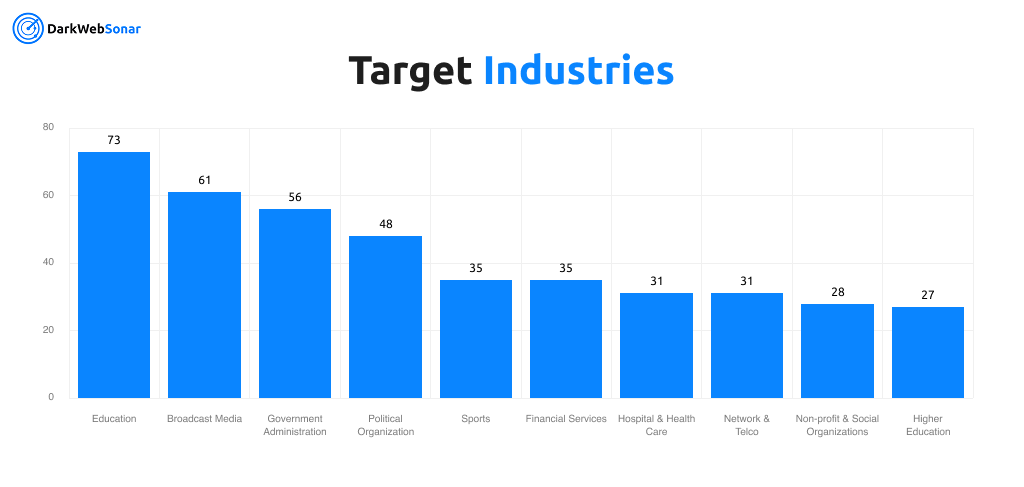
Notable sector distribution:
- Public sector: Government Administration, Political Organizations, Government & Public Sector
- Media & Information: Broadcast Media, Newspapers & Journalism, Online Publishing
- Education: Education, Higher Education/Academia
- Critical services: Healthcare & Pharmaceuticals, Hospital & Health Care, Network & Telecommunications
The emphasis on media, government, and education sectors aligns with hacktivist strategies designed to maximize propaganda value and public awareness, while the inclusion of critical infrastructure suggests an intent to demonstrate capability and generate operational disruption.
Tactics, Techniques & Procedures (TTPs)
Primary Attack Strategy
- DDoS dominance: Over 97% of logged incidents are denial-of-service attacks targeting web infrastructure
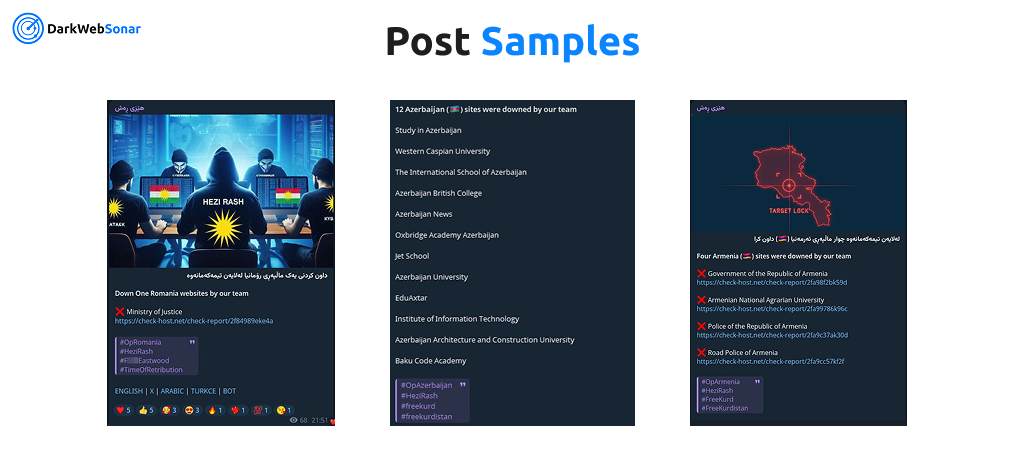
- Telegram coordination: Primary operational communication occurs through Telegram channels for campaign announcements and proof-of-attack sharing
- High-frequency operations: Sustained daily attack volumes with spikes exceeding 50+ incidents in single days
- Multi-vector disruption: Targets web services, APIs, and network infrastructure simultaneously
Secondary Methods
- Website defacements: Occasional defacements with propaganda messaging (7 incidents)
- Data breach claims: Limited data exfiltration operations (3 incidents)
- Initial access attempts: Reconnaissance and credential compromise efforts (6 incidents)
Coordination & Communication
- Telegram presence: 852 incidents tracked through Telegram announcements and channel postings
- Public proof-of-attack: Screenshots and service outage claims shared for credibility and visibility
- Campaign synchronization: Coordinated multi-target strikes during peak activity periods
Motivation
- Blend of ideological hacktivism and operational disruption
- Focus on symbolic and high-visibility targets across media, government, and critical infrastructure
- Geopolitical dimension with heavy targeting of Middle Eastern, European, and Western nations
Notable Campaigns / Victims
HEZI RASH's rapid operational tempo has produced numerous high-impact campaigns since their emergence in July 2025:
- October 2025 surge: Massive spike in activity with 104 incidents on October 9–10, 2025, targeting government and media infrastructure across multiple countries
- Education sector targeting: 73 incidents against educational institutions, including universities and school systems in Turkey, Azerbaijan, Israel, and Western nations
- Media infrastructure: 61 incidents targeting broadcast media organizations, reflecting a strategy of disrupting information channels
- Government targets: Sustained campaigns against government administration (56 incidents) and political organizations (48 incidents) across Middle Eastern and European nations
- Healthcare disruption: 45 total incidents against healthcare providers, including hospitals and pharmaceutical companies
The group's telegram-driven model enables rapid scaling and coordination, with incidents often announced and amplified through social media channels to maximize visibility and psychological impact.
Evolution & Trends
- Emergence: First observed July 16, 2025, with immediate high-volume activity
- Growth trajectory: Rapid escalation from initial sightings to sustained daily operations exceeding 25+ incidents
- Peak activity: October 9–10, 2025 represented the highest concentration with 104 incidents in 48 hours
- Operational maturity: Sustained activity through November 2025 demonstrates organizational capacity for long-term campaigns
- Activity pattern: Spiked activity level indicates coordinated bursts followed by consistent baseline operations
HEZI RASH's short but intense operational history suggests a well-resourced collective that rapidly established infrastructure and coordination channels, enabling immediate high-impact operations rather than gradual scaling typical of nascent hacktivist groups.
DarkWebSonar Insights
Our telemetry reveals unique aspects of HEZI RASH's operations:
- DDoS specialization: Overwhelming focus on denial-of-service tactics (97.4% of incidents) distinguishes them from ransomware groups and mixed-operation actors
- Geographic diversity: 38 victim countries demonstrate global reach and opportunistic targeting beyond regional boundaries
- Telegram amplification: 852 incidents tracked through Telegram channels highlight the platform's central role in coordination and propaganda
- Industry targeting strategy: Emphasis on education, media, and government sectors maximizes visibility and public awareness
- Rapid scaling: From zero to 856 incidents in under four months reflects highly organized infrastructure and operational capacity
Unlike quarterly threat reports, DarkWebSonar provides real-time tracking of HEZI RASH's victim announcements, enabling early warning when organizations are targeted, often before public disclosure or service impact confirmation.
The group's spiked activity timeline shows clear peaks during October 2025, with sustained operations suggesting ongoing campaign planning and execution capabilities that extend beyond isolated events.
Threat Intelligence Indicators
Attack Progression Pattern
- Target selection based on symbolic value, visibility, and infrastructure vulnerability
- Campaign announcement via Telegram channels to coordinate and amplify impact
- Coordinated DDoS launch targeting web infrastructure, APIs, and network services
- Proof-of-attack posting with screenshots and service disruption claims for propaganda value
- Follow-on activity: Occasional defacements or breach claims to maintain momentum
Operational Characteristics
- Telegram-driven coordination: Primary command and control through public and semi-public Telegram channels
- High-frequency operations: Capable of sustaining 25–50+ incidents per day during peak periods
- Multi-continent reach: Infrastructure and targeting span Europe, Asia, Middle East, and Americas
- Symbolic targeting: Preference for government, media, and education sectors that generate public attention
Notable Geopolitical Patterns
- Middle Eastern focus: Heavy concentration on Azerbaijan (167), Turkey (105), Israel (75), Iran (70), Iraq (59), Syria (47)
- Western targeting: Significant operations against Germany (52), USA (40), UK (24), Canada (13)
- Asian campaigns: Notable activity against Japan (72), Pakistan (14), and other Asian nations
Outlook
HEZI RASH shows no signs of operational decline as of November 2025. With 856 incidents logged in just over three months and sustained activity through late 2025, the group demonstrates the capacity for long-term disruptive campaigns.
Their telegram-driven model enables rapid scaling and coordination, while their focus on DDoS attacks provides a low-barrier, high-impact methodology that can be sustained indefinitely with minimal technical requirements.
Organizations in government, media, education, and critical infrastructure sectors across the Middle East, Europe, and North America remain at elevated risk, particularly during periods of geopolitical tension or high-visibility events.
The group's proven ability to maintain consistent operational tempo, coordinate multi-target campaigns, and amplify impact through social media channels positions them as a serious and persistent threat for the remainder of 2025 and beyond.
Conclusion
HEZI RASH exemplifies how modern hacktivist collectives leverage telegram coordination and DDoS specialization to achieve high-impact disruption with minimal technical sophistication. Their rapid emergence from July 2025 to one of the most active groups tracked by DarkWebSonar underscores the evolving threat landscape where hacktivism and cyber disruption remain persistent risks to organizations globally.
With 856 incidents in under four months and sustained activity across 38 countries, HEZI RASH demonstrates that high-frequency, symbolically-targeted attacks can generate significant operational impact even without the deep technical compromise typical of ransomware operations.
The group's emphasis on media, government, and education sectors reflects a strategic approach to maximizing visibility and public awareness, while their global reach ensures that organizations across multiple continents must remain vigilant against coordinated disruption campaigns.
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar's continuous monitoring of hacktivist groups and ransomware leak sites. Want real-time visibility into actors like HEZI RASH? Contact Sales.