
- Name: DarkStorm Team
- Type: Hacktivist Collective (Pro-Palestinian)
- First Seen: Late 2023
- Last Seen: Active in 2025
- Risk Level: High
Introduction
DarkStorm Team has quickly emerged as one of the most disruptive hacktivist collectives of 2025. Known for large-scale DDoS campaigns and politically motivated cyberattacks, the group positions itself as part of the “digital resistance” in support of Palestine.
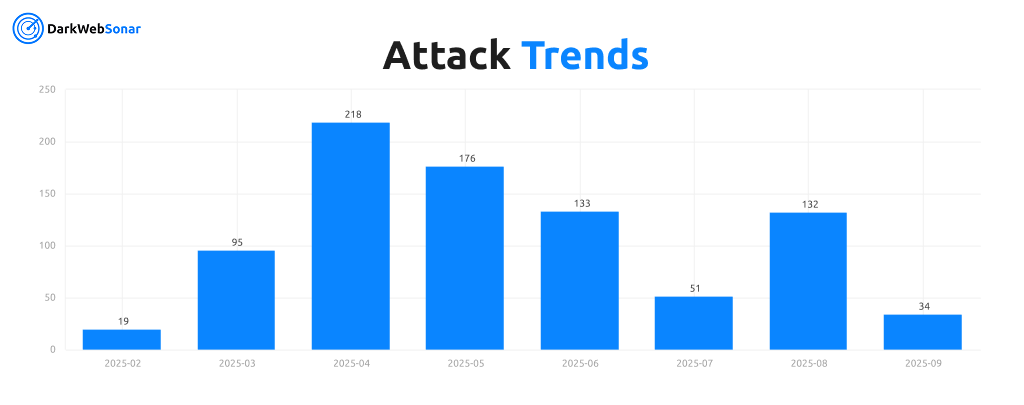
DarkWebSonar tracked 828 entries in 2025 linked to DarkStorm Team, making them one of the most prolific actors we monitor. Their activity surged in spring 2025 before stabilizing at a consistently high level.
By the Numbers (DarkWebSonar Data)
- Total entries (2025 YTD): 828
- Activity trend: Peak in April 2025 (218 entries) with sustained high volume through summer
Attack type distribution:
DarkStorm Team’s operational profile is overwhelmingly skewed toward DDoS attacks, which account for more than 95% of their observed activity. This heavy reliance on denial-of-service tactics underscores their strategy of disruption and visibility rather than deep technical compromise.
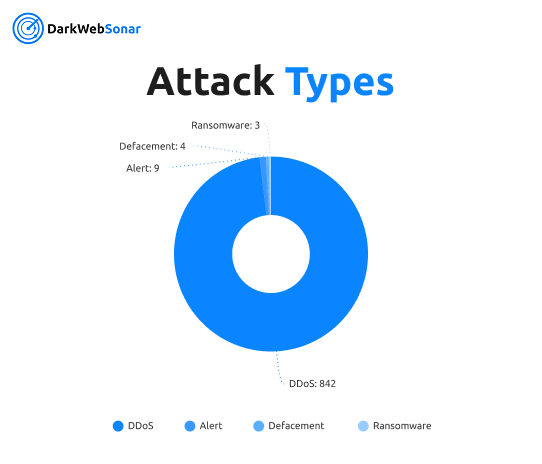
The handful of defacements and ransomware attempts appear opportunistic, used to amplify propaganda or experiment beyond their core competency. Alerts, noise, and other minor incidents further highlight that while DarkStorm occasionally dabbles in different techniques, their impact comes almost exclusively from high-volume DDoS campaigns designed to overwhelm infrastructure and attract media attention.
Top targeted countries (2025):
The actor’s targeting shows a clear geopolitical dimension. Israel and the United States dominate the victim list, reflecting the group’s pro-Palestinian stance and opposition to Western allies.
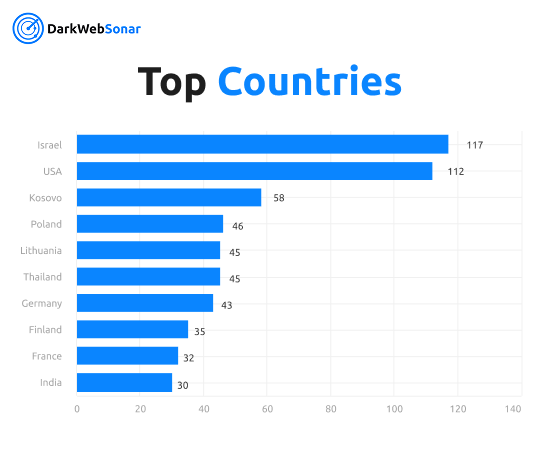
Beyond these, attacks spread across Europe (Poland, Lithuania, Germany, France) and Asia (Thailand, India, Turkey), highlighting opportunistic campaigns designed for reach and visibility. The inclusion of Kosovo as a frequent target underlines their focus on politically symbolic regions, while the broad geographic mix reinforces DarkStorm’s role as a disruptive, globally oriented hacktivist collective.
Tactics, Techniques & Procedures (TTPs)
Primary Attack Strategy
- DDoS dominance: Over 95% of logged incidents are denial-of-service attacks
- Target focus: Governments, airports, financial institutions, and media outlets
- Symbolic disruption: Attacks often coincide with politically sensitive events in the Middle East
Secondary Methods
- Opportunistic ransomware and breach attempts
- Website defacements with propaganda messaging
- Data leak claims to boost credibility
Coordination & Communication
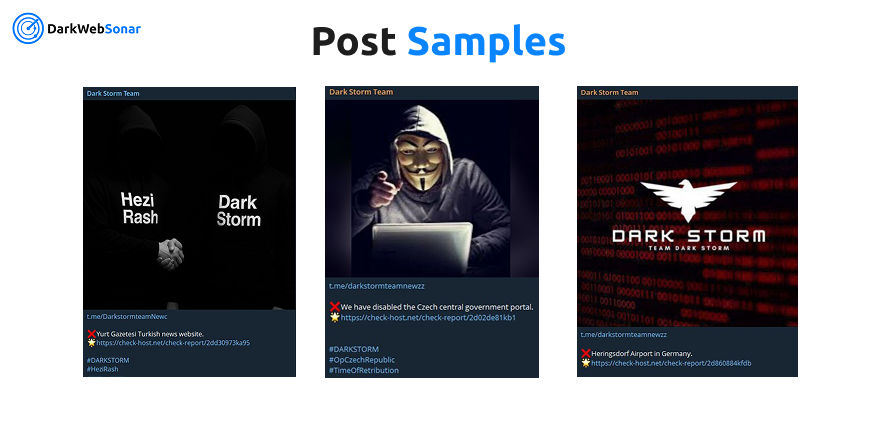
- Channels: Telegram groups where they announce campaigns and share “proof” of disruption
- Alliances: Messaging overlaps with Anonymous Sudan and Ghosts of Palestine, plus operational similarities to Russian-affiliated Killnet
Motivation
- Pro-Palestinian stance, framed as “digital resistance” against Israel and allies
- Blend of ideological protest and cybercrime-for-profit (selling attack services and stolen data)
Notable Campaigns / Victims
- X (Twitter) – March 2025, massive DDoS causing disruption for 40,000+ users worldwide
- John F. Kennedy & LAX Airports – 2024, denial-of-service targeting air transport hubs
- UAE Ministry of Education – June 2024, breach and service disruption tied to anti-UAE stance
- Israeli Government Sites – July 2025, coordinated DDoS wave during Gaza conflict escalation
Evolution & Trends
- Origins: Emerged late 2023 following the October 7 Hamas-led attack on Israel
- Growth: Exploded in early 2025, peaking at over 200 logged incidents in April
- Trajectory: While monthly activity has dipped since the spring peak, DarkStorm remains consistently active across multiple geographies
- Geopolitical links: Suspected collaboration with pro-Russian actors, based on shared tools and attack overlaps
DarkWebSonar Insights
Our telemetry highlights unique aspects of DarkStorm Team’s operations:
- DDoS dominance: Overwhelming reliance on volumetric attacks for impact and visibility
- Global opportunism: Target set spans NATO states, Middle Eastern governments, and symbolic global entities
- Persistence: Despite fluctuations, DarkStorm sustains monthly operations with broad reach
- Propaganda amplification: Effective use of Telegram and media attention to magnify psychological and reputational impact
Unlike generic summaries, DarkWebSonar’s real-time dataset lets us quantify monthly attack volumes, identify top victim countries, and correlate spikes with geopolitical flashpoints.
Threat Intelligence Indicators
Attack Progression Pattern
- Target announcement on Telegram or hacktivist forums
- Coordinated DDoS launch, often amplified by botnet-for-hire services
- Proof-of-attack posting (screenshots, outage claims) for propaganda value
- Follow-on activity: occasional defacements or opportunistic ransomware attempts
Notable Geopolitical Themes
- Opposition to Israel and U.S. policy
- Targeting of NATO-aligned countries (Poland, Lithuania, Germany)
- Regional campaigns in the Middle East (UAE, Turkey, Egypt, Iran)
Outlook
DarkStorm Team is expected to remain highly active throughout 2025, particularly during geopolitical escalations involving Israel, NATO, and Middle Eastern governments. Their reliance on DDoS makes them disruptive but not deeply sophisticated — however, their scale, consistency, and symbolic target selection ensure they remain a serious operational risk.
Risk Level: High
Conclusion
DarkStorm Team blends hacktivism and disruption with propaganda value, weaponizing the dark web and Telegram to amplify their message. Organizations in Israel, NATO countries, and Middle Eastern governments remain at highest risk.
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar’s continuous monitoring of hacktivist and ransomware groups. Want real-time visibility into actors like DarkStorm Team? Contact Sales.