
- Name: CL0P
- Type: Ransomware Group
- First Seen: October 2024
- Last Observed: November 2025
- Risk Level: Critical
Introduction
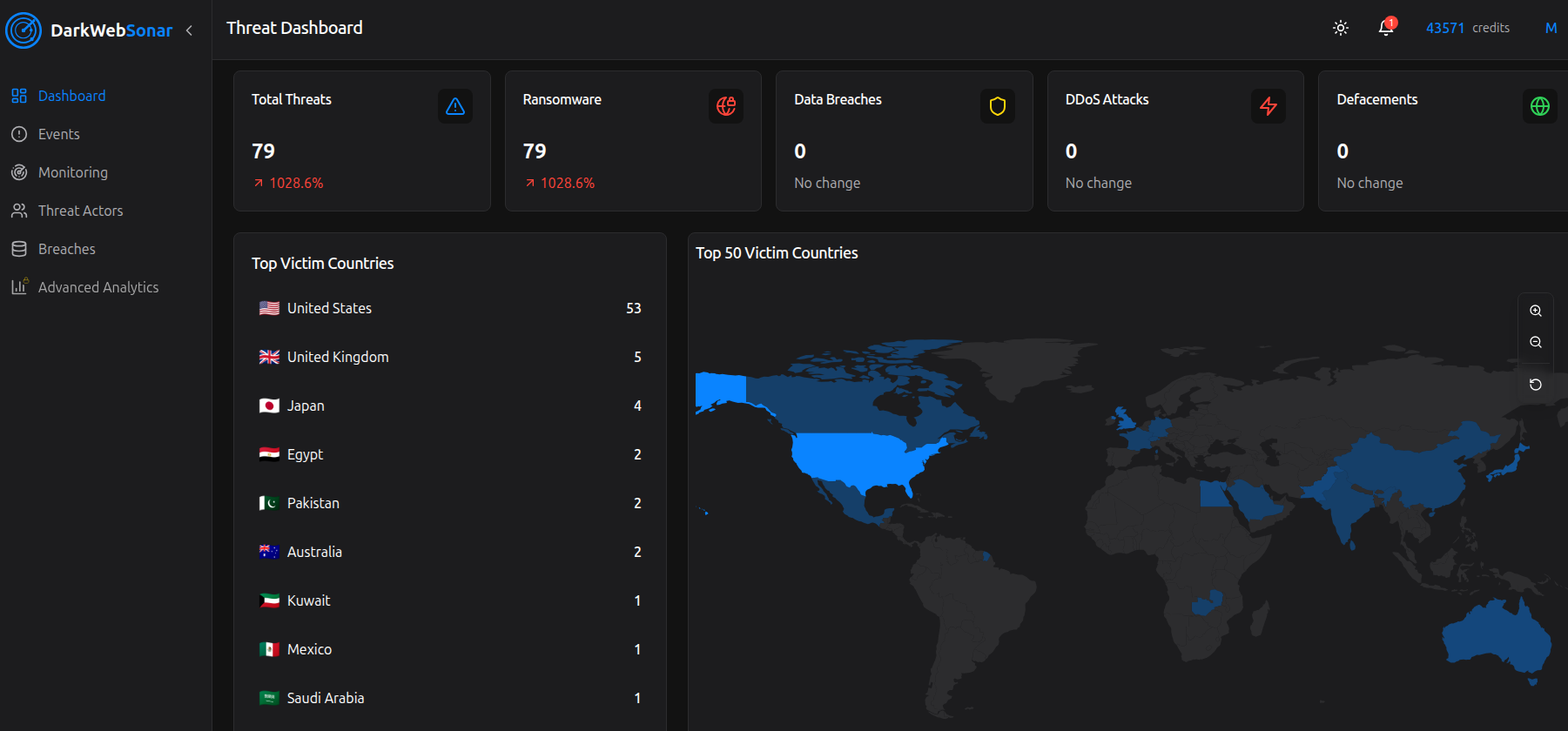
CL0P has re-emerged as one of the most dangerous ransomware and data extortion groups of 2025, with a massive surge in activity that demonstrates their continued operational sophistication. Tracked by DarkWebSonar since October 2024, the group has logged 480 confirmed victim postings, with a dramatic 1,028% increase in activity over the past 30 days based solely on leak-site telemetry. Known for their aggressive double extortion tactics, large-scale supply chain campaigns, and exploitation of zero-day vulnerabilities, CL0P represents a persistent and evolving threat to organizations worldwide.
Historically, CL0P (also written as Clop or Cl0p) is associated with the Russian-speaking TA505/FIN11 ecosystem and has been active since at least 2019, with early campaigns relying heavily on phishing and Windows-focused ransomware payloads. Over time, the group shifted toward data-theft–only extortion and mass exploitation of file transfer and enterprise platforms such as Accellion FTA, GoAnywhere MFT, MOVEit, Cleo, Fortra, and most recently Oracle E‑Business Suite (EBS).
DarkWebSonar’s 2024–2025 telemetry shows that this evolution has not reduced their impact, instead, it has enabled CL0P to scale their victim count dramatically through systemic, software-supply-chain–style campaigns.
By the Numbers (DarkWebSonar Data)
- Total victims (Oct 2024–Nov 2025): 480
- Recent activity (last 30 days): 79 victims
- Activity growth: 1,028% increase compared to previous 30‑day period
- Risk score (DarkWebSonar): 114 (Critical)
DarkWebSonar’s dataset is based on observed victim postings on CL0P’s leak site, not on incident reports or telemetry from endpoint or network sensors. This means the numbers below likely underestimate the true number of intrusions, as some victims pay silently or are never listed.
Attack type distribution
Within the DarkWebSonar dataset, CL0P’s activity appears almost exclusively focused on ransomware / data extortion operations, with 479 of 480 logged entries involving extortion-related postings against corporate victims.
This aligns with external reporting that describes CL0P today primarily as a data extortion operation, sometimes without deploying a traditional file-encrypting payload at all.
Top targeted industries
CL0P demonstrates a diverse but highly strategic targeting approach, focusing on industries where operational disruption and data sensitivity create strong leverage for extortion:
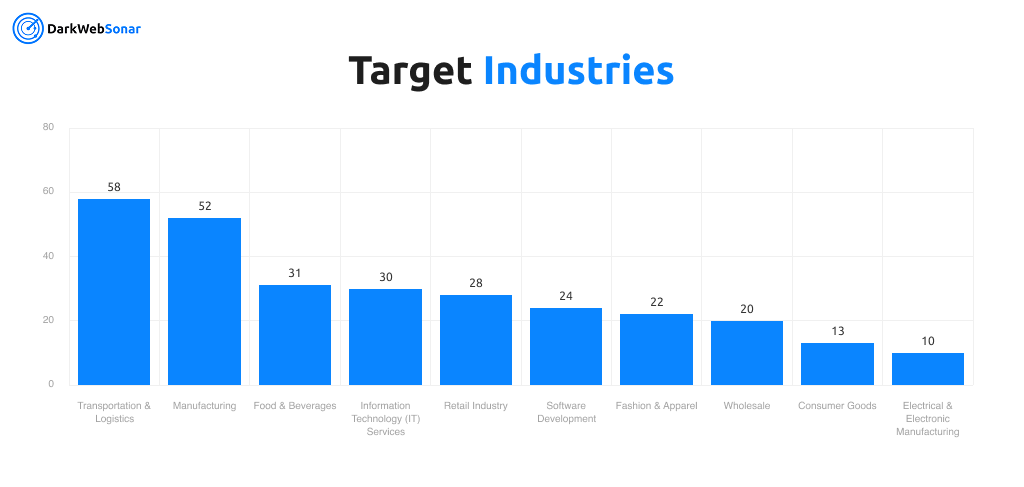
This targeting pattern reflects CL0P’s understanding that supply chain disruption, just‑in‑time operations, and tight margins create maximum pressure for ransom payments. Transportation, manufacturing, and retail sectors are particularly vulnerable due to their reliance on continuous operations and complex partner ecosystems. External analysis of CL0P’s MOVEit, Cleo, and Oracle campaigns confirms that a large proportion of their victims sit at critical junctions in global supply chains.
Top targeted countries
DarkWebSonar’s victim distribution shows an overwhelming focus on the United States, which accounts for 73.75% of all observed postings (354 out of 480):
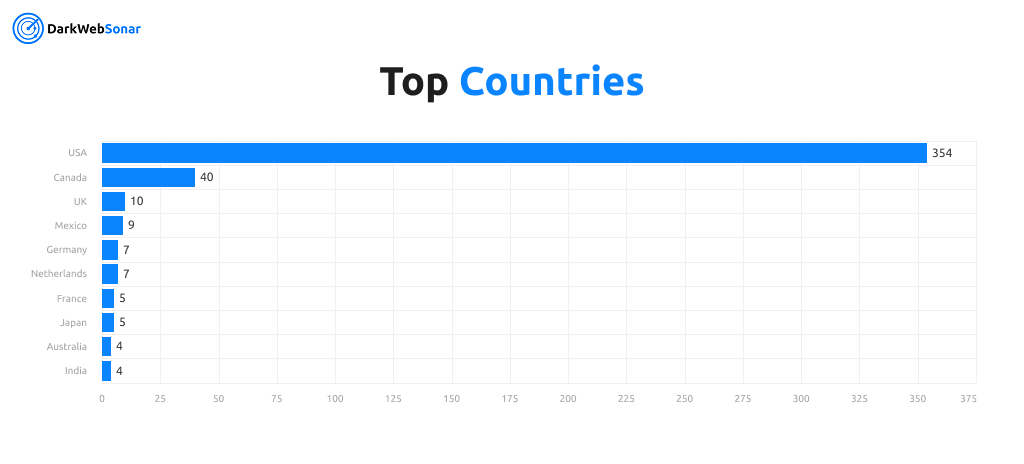
Beyond North America and Europe, CL0P has also posted victims from Mexico, China, Spain, Italy, and other regions, demonstrating global reach while maintaining a primary focus on Western enterprises with strong financial capabilities. External sources corroborate this Western‑enterprise focus and highlight the group’s repeated targeting of large U.S. and European organizations across healthcare, government services, finance, and technology.
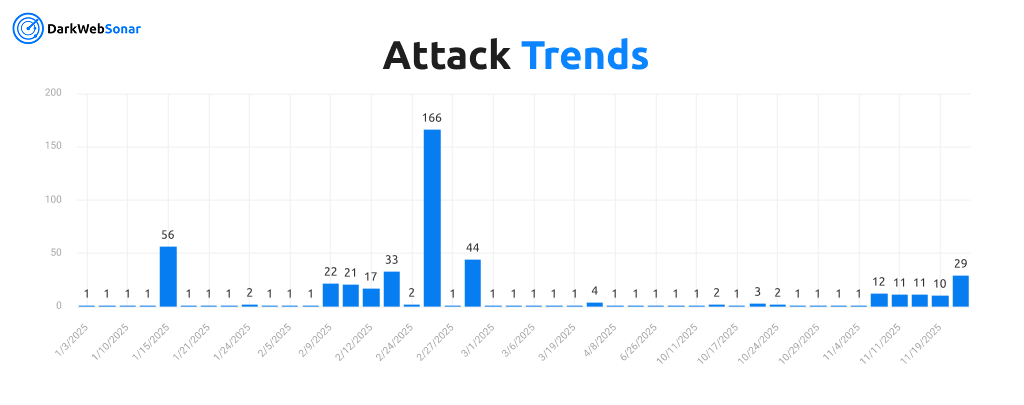
Activity timeline highlights
- October 3, 2024: First observed victim posting in DarkWebSonar dataset
- January 15, 2025: Major activity spike with 56 victims posted in a single day
- February 9–13, 2025: Sustained campaign with 22, 21, 17, and 33 postings respectively
- February 25, 2025: Largest single‑day spike with 166 victims posted
- February 28, 2025: Continued high activity with 44 victims
- November 2025: Recent resurgence with 12, 11, 11, 10, and 29 victims across several days, indicating renewed operational tempo
The February 2025 spike represents one of the largest single‑day extortion campaigns tracked by DarkWebSonar, strongly suggesting either:
- a coordinated multi‑victim exploitation campaign (mass exploitation of a shared technology stack), or
- batch publication of victims compromised during a prior intrusion window.
This behavior is consistent with CL0P’s historical playbook, where mass exploitation of a single zero‑day across a widely used platform (e.g., MOVEit, Accellion FTA, Cleo, Oracle EBS) is followed by staged victim naming and extortion over weeks or months.
Tactics, Techniques & Procedures (TTPs)
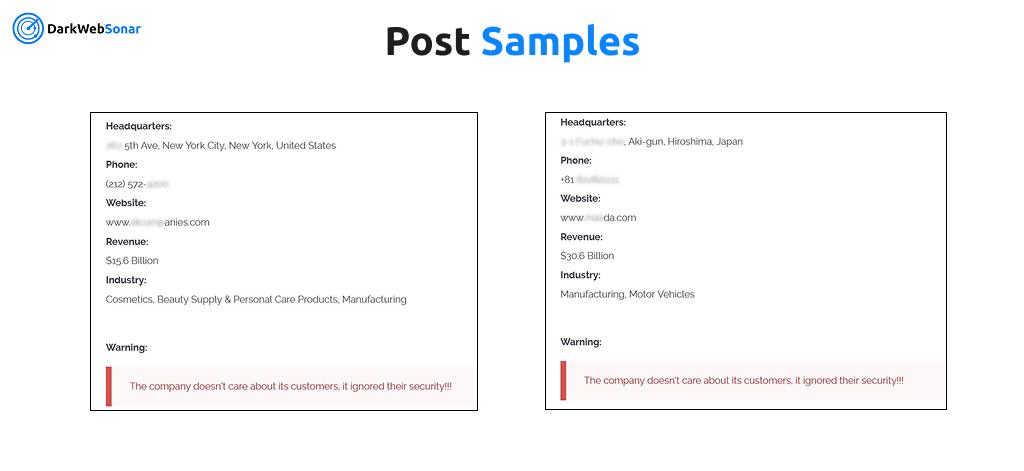
Extortion Strategy
- Double / multi‑pronged extortion: Traditionally combines file encryption with data exfiltration and public leak threats; in recent campaigns, CL0P has frequently prioritized data theft and extortion without encryption, especially during supply‑chain zero‑day exploitation campaigns.
- Tor‑based leak site: Maintains a dedicated dark web portal for victim shaming and data publication (often branded “CL0P^_-LEAKS”).
- Escalation tactics: Progresses from private negotiations to public data releases with countdown timers, staged data dumps, and direct outreach to media, partners, and customers to increase pressure.
- Selective high‑value targeting: Focuses on organizations with significant revenue, rich datasets, and high operational disruption costs; external reporting repeatedly notes CL0P’s emphasis on large enterprises and public‑sector entities.
Initial Access Methods
DarkWebSonar only observes post‑compromise victim postings, but external technical reporting provides a detailed view of how CL0P and associated clusters gain initial access:
- Zero‑day vulnerability exploitation (signature MO):
- 2021–2023: Accellion FTA, GoAnywhere MFT, MOVEit Transfer zero‑days (e.g., CVE‑2023‑34362) used to compromise hundreds of organizations in single campaigns.
- 2024–2025: Continued focus on managed file transfer and integration platforms, including Cleo products (CVE‑2024‑50623 / CVE‑2024‑55956) and Oracle E‑Business Suite BI Publisher Integration (CVE‑2025‑61882 and likely CVE‑2025‑61884).
- Supply chain and “one‑to‑many” attacks: Targets third‑party platforms and service providers (MFT, ERP, integration middleware, MSPs) to gain access to large downstream victim populations with identical vulnerabilities.
- Compromised credentials: Uses credentials harvested from infostealer logs and compromised business email accounts to send convincing extortion and phishing emails from legitimate infrastructure.
- Phishing and malspam: Earlier campaigns (2019–2022) relied heavily on mass phishing and spear‑phishing to deploy loaders like Truebot, Cobalt Strike beacons, and other tools prior to ransomware execution.
Technical Capabilities
- Ransomware payloads:
- Windows‑focused ransomware family derived from CryptoMix/CrypBoss; encrypts files and appends extensions like .clop, .CL0P, CIIp, C_L_O_P, etc.
- A Linux variant appeared around late 2022, though early analysis suggested flaws that sometimes allowed decryption.
- Data exfiltration:
- Systematic theft of sensitive files and databases before any encryption step.
- Use of custom tools such as Teleport for large‑scale data exfiltration, alongside common red‑team tooling (Cobalt Strike, web shells such as DEWMODE/LEMURLOOT, SDBot, FlawedAmmyy RAT).
- Lateral movement & privilege escalation:
- Tools and techniques such as Mimikatz, PsExec, and Cobalt Strike to traverse networks, dump credentials, and gain domain‑wide privileges.
- Persistence & evasion:
- Disables security controls (e.g., Windows Defender, backup agents), uses obfuscation, and maintains a minimal footprint, especially in pure data‑extortion campaigns where encryption is skipped to reduce detection risk.
Business Model & Operations
- Affiliates and ecosystem links: Historically described as Ransomware‑as‑a-Service (RaaS) and closely tied to TA505/FIN11, with multiple overlapping clusters sharing infrastructure and payloads. Public reporting suggests today’s CL0P operations blend:
- a core team controlling leak infrastructure, tooling, and negotiations, and
- associated intrusion operators (e.g., FIN11/Graceful Spider–linked clusters) executing mass exploitation and intrusion activity.
- High‑value targeting: Prioritizes enterprises with revenues in the tens or hundreds of millions, where downtime and data exposure translate into strong incentives to pay.
- Strategic timing: Frequently aligns mass exploitation with unpatched zero‑days, exploiting the short window between first exploitation and vendor patch / customer rollout.
Notable Campaigns / Victims
MOVEit Exploitation (2023)
CL0P gained global attention for the 2023 exploitation of a zero‑day in Progress Software’s MOVEit Transfer platform (CVE‑2023‑34362). This campaign affected hundreds of organizations worldwide, including government agencies, financial institutions, healthcare providers, and major enterprises. Public reporting on MOVEit victims (e.g., Maximus, numerous U.S. and European agencies, and major private‑sector firms) illustrates CL0P’s ability to:
- weaponize previously unknown vulnerabilities quickly,
- pivot from initial access to mass data theft, and
- run large‑scale, multi‑month extortion operations based on a single technology stack.
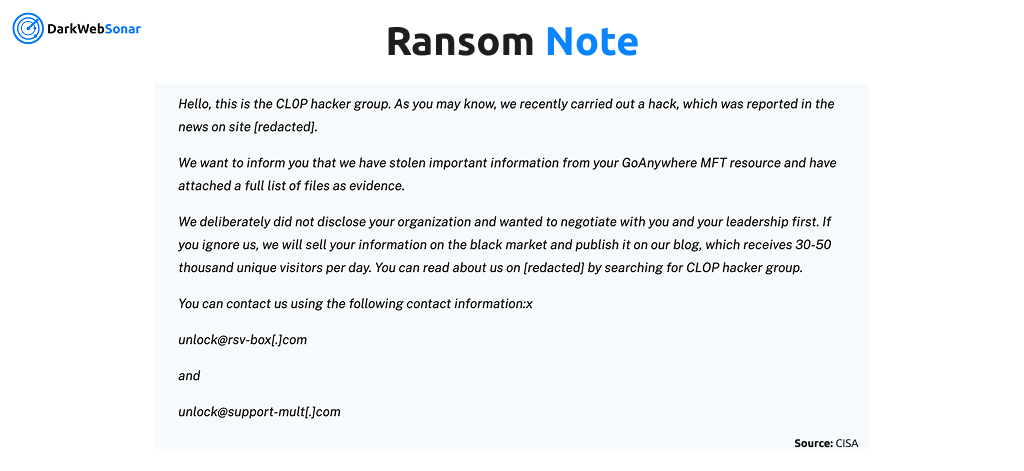
Cleo / GoAnywhere / Fortra Campaigns (2023–2024)
Following MOVEit, CL0P continued to target managed file transfer and integration platforms, including GoAnywhere MFT, Cleo products, and Fortra file transfer solutions. These campaigns reinforced a pattern:
- identify a widely deployed enterprise file transfer / integration product,
- develop or acquire a working exploit (sometimes zero‑day, sometimes n‑day but under‑patched),
- compromise large numbers of organizations in a short window, and
- slow‑roll victim postings on the leak site over subsequent weeks and months.
Oracle E‑Business Suite Zero‑Day (2025)
In 2025, CL0P (and/or closely associated clusters) were linked to mass exploitation of a zero‑day vulnerability in Oracle E‑Business Suite:
- Vulnerability: CVE‑2025‑61882 (BI Publisher Integration in Oracle Concurrent Processing, CVSS 9.8), with indications that CVE‑2025‑61884 is also part of the exploit chain.
- Scope: Affects Oracle EBS versions 12.2.3 to 12.2.14 and potentially older unsupported versions.
- Timeline:
- Suspicious activity and exploitation observed as early as July–August 2025, before patches were available.
- Oracle advisory and patch release in early October 2025.
- Mass extortion emails sent from compromised third‑party email accounts starting late September 2025, claiming CL0P branding and threatening data leaks.
- Victims: Public reports mention nearly 30 named organizations on CL0P’s leak site, including major enterprises and public‑sector entities; follow‑on reporting highlights victims such as GlobalLogic, UK NHS organizations, and others notified of Oracle EBS–related data theft.
This campaign closely mirrors CL0P’s MOVEit playbook: mass exploitation of a strategically positioned enterprise platform, delayed extortion notifications, and staged victim naming on the leak site. DarkWebSonar’s February and November 2025 spikes strongly align with this Oracle‑linked wave of postings.
Targeting Patterns (DarkWebSonar + external)
Cross‑referencing DarkWebSonar victim telemetry with public reporting reveals several recurring themes:
- Critical supply chain nodes: logistics providers, manufacturers, MSPs, and integration service providers feature heavily both in DarkWebSonar’s top‑industry list and in public disclosures.
- Public sector & healthcare: especially during MOVEit and Oracle campaigns, with victims including contractors handling government data and national healthcare systems.
- High‑value data concentration: sectors that hold large volumes of PII, financial records, or sensitive IP (e.g., finance, healthcare, tech, government contractors) are repeatedly over‑represented among public victims.
Evolution & Trends
- Long‑running operation: First detected in 2019, CL0P is one of the longest continuously operating cyber extortion brands, maintaining a dark web leak site since around December 2020.
- Shift from classic ransomware to data extortion: Since 2021, CL0P has increasingly de‑emphasized encryption in favor of pure data theft and extortion, especially in large supply‑chain campaigns. DarkWebSonar’s dataset captures the outcome of this shift: a high volume of victim postings linked to mass exploitation waves rather than isolated, bespoke intrusions.
- Mass exploitation as a business model: Public sources and DarkWebSonar telemetry both show that CL0P’s most impactful campaigns are built on mass exploitation of critical services, rather than one‑off intrusions.
- Operational resilience: Despite law‑enforcement actions and periods of reduced visibility, CL0P and affiliated clusters have repeatedly resurfaced with new campaigns (Accellion > GoAnywhere/Fortra > MOVEit > Cleo > Oracle EBS).
- Recent growth trajectory: DarkWebSonar’s observed 1,028% month‑over‑month activity increase underscores how quickly CL0P can pivot from relative quiet to sustained high‑tempo operations when a new high‑impact vulnerability is identified.
DarkWebSonar Insights
Unlike traditional incident‑driven reporting, DarkWebSonar tracks CL0P’s victim postings in real time directly from their leak infrastructure. This enables:
- Granular targeting insight: Real‑time visibility into which industries, geographies, and organization sizes CL0P is actively extorting at any given moment.
- Spike detection: Immediate identification of coordinated campaigns, such as the February 25, 2025 and November 2025 posting surges that align with major exploitation waves.
- Early warning: Victim announcements on CL0P’s leak site often appear before public disclosure, regulatory filings, or service‑impact confirmation, giving defenders and third‑party risk teams an earlier signal that a given organization has been compromised.
- Trend analysis: Continuous monitoring of changes in operational tempo, target selection, and geography—essential for understanding whether CL0P is ramping up, pausing, or shifting focus.
- Vulnerability correlation: Ability to correlate spikes in new victim postings with public disclosures and vendor advisories (e.g., MOVEit and Oracle EBS zero‑days), enabling faster assessment of which technologies are currently being weaponized.
DarkWebSonar’s telemetry offered early confirmation that CL0P’s Oracle EBS campaign had moved from isolated incidents to mass exploitation, days before many victims publicly acknowledged impact.
Threat Intelligence Indicators
Key Vulnerabilities Exploited (Selected)
- CVE‑2023‑34362 – MOVEit Transfer SQL injection vulnerability (2023 campaign; mass exploitation and data theft).
- CVE‑2024‑50623 / CVE‑2024‑55956 – Vulnerabilities in Cleo software products exploited in 2024–2025 campaigns.
- CVE‑2025‑61882 / CVE‑2025‑61884 – Oracle E‑Business Suite BI Publisher / related vulnerabilities exploited as a zero‑day at scale in 2025.
DarkWebSonar victim spikes around February and late 2025 align with public reporting around these mass exploitation events.
Typical Attack Progression Timeline
- Initial compromise via zero‑day exploitation against file transfer / ERP platforms, credential theft from infostealer logs, or (less commonly today) phishing / malspam campaigns.
- Lateral movement and privilege escalation using tools such as Cobalt Strike, Mimikatz, PsExec, and custom loaders.
- Data discovery and exfiltration of sensitive files, databases, and mail stores, often using tools like Teleport or bespoke scripts.
- (Optional) Ransomware deployment across Windows (and occasionally Linux) systems to maximize business disruption.
- Leak site posting with victim details and sample data on the CL0P Tor portal.
- Extortion and negotiation via Tor‑hosted chat portals, email, or compromised business email accounts, often with countdown timers and threats of public data release or harassment campaigns.
Operational Indicators
- Tor‑based leak infrastructure branded around CL0P / CL0P^_-LEAKS.
- Batch publication patterns (large clusters of new victims added in a single day).
- High‑value, Western enterprise focus with disproportionate representation of U.S. organizations.
- Recurring targeting of file‑transfer, integration, and ERP technologies as initial access vectors.
Outlook
CL0P’s recent surge in DarkWebSonar telemetry (1,028% growth over the last 30 days) and continued reliance on high‑impact zero‑day exploitation position them as a critical global threat for the remainder of 2025 and into 2026. External reporting consistently ranks CL0P among the most active and damaging ransomware / extortion operations, frequently outpacing or rivaling groups such as LockBit, Akira, and RansomHub in victim volume during peak quarters.
Given CL0P’s:
- proven capability to identify and weaponize new vulnerabilities quickly,
- preference for systemic, one‑to‑many attacks against critical enterprise platforms, and
- focus on large, data‑rich organizations in the U.S., Canada, and Europe,
organizations running managed file transfer solutions, ERP platforms (especially Oracle EBS), and integration middleware should assume they are priority targets.
Priority defensive actions include:
- Aggressive patch management for MFT, ERP, and integration platforms, especially when zero‑day advisories mention active exploitation by CL0P‑linked actors.
- External attack surface monitoring to rapidly detect exposed file transfer portals, admin interfaces, and misconfigured services.
- Deep inspection of outbound data flows from these systems to spot unusual data exfiltration activity.
- Hardened identity and email security, including monitoring for compromised third‑party accounts used in extortion or phishing campaigns.
Conclusion
CL0P exemplifies how established ransomware and extortion operations can re‑emerge with renewed scale and sophistication after periods of apparent quiet. DarkWebSonar’s telemetry, 480 victim postings between October 2024 and November 2025, including a 1,028% month‑over‑month surge shows that CL0P remains one of the most operationally relevant threat actors of 2025.
Their strategic focus on U.S. and Western enterprises, supply‑chain and platform‑level vulnerabilities, and zero‑day mass exploitation ensures that a single unpatched system can expose hundreds of organizations. External intelligence on MOVEit, Cleo, and Oracle EBS campaigns strongly validates the trends observed in DarkWebSonar’s data.
For defenders, DarkWebSonar’s real‑time visibility into CL0P’s leak‑site activity offers a unique, victim‑centric vantage point: it reveals not only who is being targeted, but which technologies and supply chains are currently under active exploitation. Combined with timely patching and vigilant monitoring, this perspective is critical for reducing exposure to one of today’s most dangerous extortion groups.
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar’s continuous monitoring of ransomware leak sites. Want real‑time visibility into groups like CL0P? Contact Sales.