
- Name: Akira
- Type: Ransomware Group
- First Seen: October 2024
- Last Seen: September 2025
- Risk Level: High
Introduction
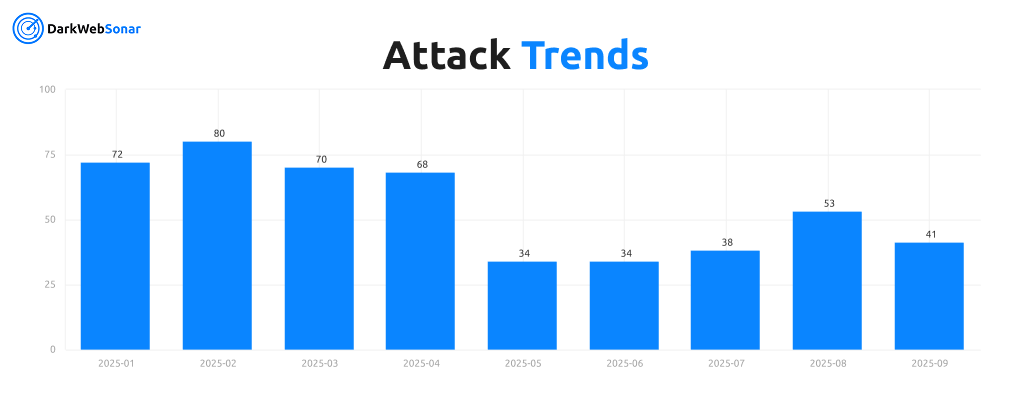
Akira has quickly risen to prominence as one of the most active ransomware groups of 2025. First observed in October 2024, the group has already logged 575 incidents in DarkWebSonar’s dataset, with the vast majority being ransomware operations.
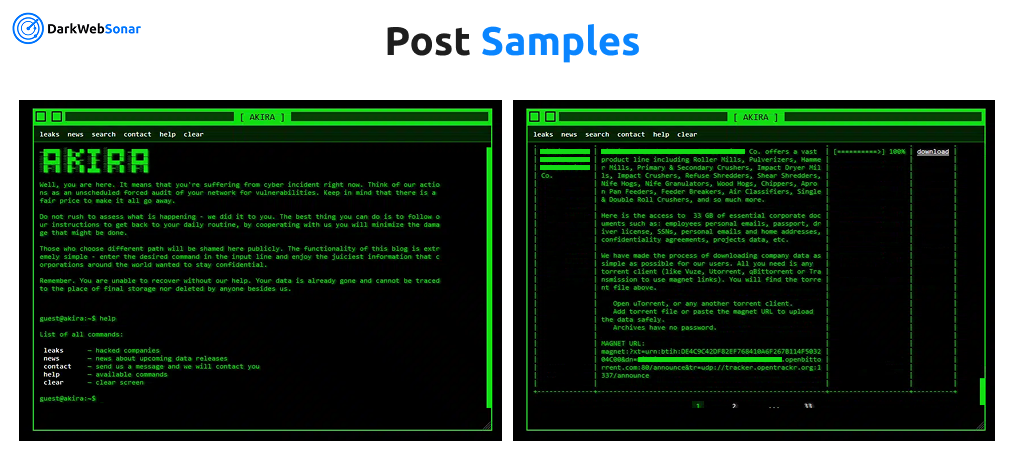
Known for its double extortion strategy and frequent use of compromised VPN credentials and RDP services, Akira has become a formidable threat to organizations across North America and beyond. The group has been profiled by agencies including CISA, which highlighted their technical sophistication and aggressive targeting campaigns.
By the Numbers (DarkWebSonar Data)
- Total incidents (Oct 2024–Sept 2025): 575
- First seen: October 3, 2024
- Major spike: January 31, 2025 (34 incidents in a single day)
- Sustained high activity through spring and summer 2025
Attack type distribution:
Akira’s operations are almost entirely ransomware-focused, with 574 of 575 logged incidents in our dataset involving ransomware deployments. This near-total reliance on encryption and data-leak extortion underscores their specialization compared to hacktivist groups or mixed-operation actors. The single DDoS incident observed is an outlier and highlights Akira’s singular commitment to ransomware as their core business model.
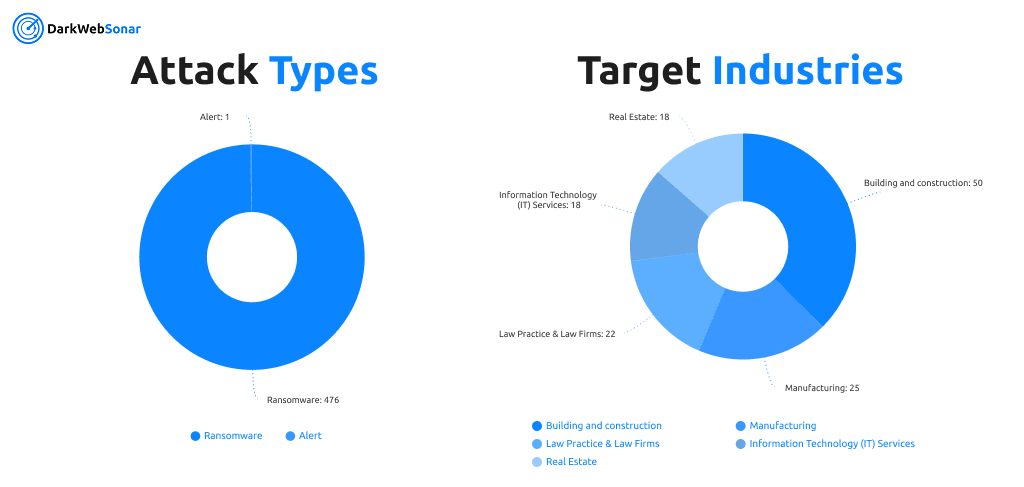
Industry targeting further emphasizes this pattern. Akira’s victims span a wide range of sectors, but construction, manufacturing, and professional services dominate their footprint. Building & construction firms alone accounted for 50 logged incidents, while law practices and IT services followed as frequent targets. Critical industries such as manufacturing, financial services, and transportation & logistics also appear prominently, reflecting Akira’s opportunistic targeting of organizations most likely to feel pressure to pay.
Top targeted countries (2025):
Akira’s victim distribution is heavily concentrated in the United States, which accounts for more than 60% of observed cases in our dataset. This reflects a strong North American focus, with the U.S. serving as the group’s primary hunting ground.
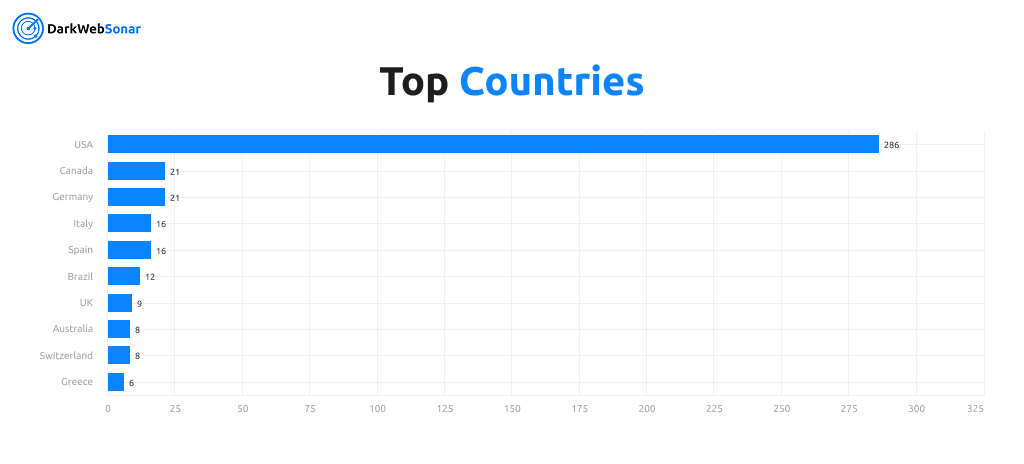
Beyond the U.S., Akira maintains a global footprint, striking victims across Europe (Germany, Spain, Italy, UK, Switzerland, Sweden) and the Americas (Canada, Brazil, Argentina). The group has also targeted organizations in Asia-Pacific regions including Australia, Singapore, and India. This global opportunism underscores Akira’s role as a ransomware collective willing to exploit vulnerabilities wherever they arise, even as its core operations remain centered on U.S.-based enterprises..
Tactics, Techniques & Procedures (TTPs)
Extortion Strategy
- Double extortion: Encrypts files while exfiltrating sensitive data for leverage
- Leak site publishing: Victim details posted on Tor-based portals to pressure payments
- Negotiation tactics: Uses sample leaks of executive data and confidential files as proof
Initial Access Methods
- Stolen VPN credentials and RDP exploitation
- Phishing campaigns delivering credential stealers and loaders
- Exploitation of known vulnerabilities, including those cited in CISA AA24-109A such as Cisco ASA/FTD flaws (CVE-2020-3259, CVE-2023-20269)
Technical Capabilities
- Cross-platform ransomware: Akira variants for Windows, Linux, and VMware ESXi
- Sophisticated encryption: Customizable encryption modes with selective file targeting
- Persistence: Use of scheduled tasks and domain administrator compromise
Business Model & Operations
- Ransomware-as-a-Service (RaaS): Affiliates earn a commission-based share of ransoms
- Targeting approach: Opportunistic but skewed toward North American enterprises
- Branding: Maintains a distinct Tor leak site with aggressive victim shaming
Notable Campaigns / Victims
- Law firms and professional services – multiple high-profile breaches, with sensitive client data leaked online
- Construction and manufacturing – Akira frequently targeted building and construction firms, with dozens of logged victims in 2025
- Education sector – victims include universities and private schools in the U.S. and Europe
- Recent notable case: CISA advisory AA24-109A detailed Akira’s attacks against organizations in critical infrastructure sectors, including healthcare and finance
Evolution & Trends
- Emergence: First active in mid-2023, but gained momentum late 2024 with rapid scaling into 2025
- Growth: By early 2025, Akira consistently ranked among the top 3 ransomware groups globally
- Trajectory: Maintains strong affiliate program and continuous variant development
- Shift in targeting: Increasingly hitting professional services, manufacturing, and critical infrastructure
DarkWebSonar Insights
Our telemetry confirms Akira’s:
- U.S. dominance: Over 60% of all known victims in our dataset are U.S.-based
- Spike activity: Major bursts of victim postings (e.g., January 31, 2025) suggest coordinated campaigns or batch leak site updates
- Industry targeting: Construction, manufacturing, and professional services among top sectors
- Affiliate-driven model: Activity patterns suggest multiple operators publishing under the Akira brand
Unlike static quarterly reports, DarkWebSonar provides real-time tracking of Akira’s victim postings, enabling early warnings before public disclosure.
Threat Intelligence Indicators
Key Vulnerabilities Exploited
- CVE-2020-3259 – Cisco ASA VPN arbitrary file read vulnerability
- CVE-2023-20269 – Cisco VPN password brute force vulnerability
Attack Progression Timeline
- Initial compromise via stolen credentials or exploited vulnerabilities
- Lateral movement and privilege escalation across Windows and Linux systems
- Data exfiltration of sensitive files
- Ransomware deployment across servers and endpoints
- Leak site posting and ransom negotiation
Outlook
Akira shows no signs of slowing down. With a well-established affiliate program, strong U.S. targeting, and continuous technical adaptation, the group is expected to remain a top ransomware threat into late 2025. Their opportunistic targeting ensures that both small firms and large enterprises remain at risk.
Conclusion
Akira exemplifies the speed with which a new ransomware group can rise to global prominence. In less than a year, they have gone from emerging threat to one of the most prolific ransomware operators tracked by DarkWebSonar. Their double extortion tactics, technical sophistication, and relentless targeting of U.S. enterprises highlight the evolving maturity of the ransomware ecosystem.
👉 Dark Web Most Wanted profiles are powered by DarkWebSonar’s continuous monitoring of ransomware leak sites. Want real-time visibility into groups like Akira? Contact Sales.